CTF collection Vol.1
Sharpening up your CTF skill with the collection. The first volume is designed for beginner.
What does the base said?
desc
Can you decode the following?
VEhNe2p1NTdfZDNjMGQzXzdoM19iNDUzfQ==
solution
echo "VEhNe2p1NTdfZDNjMGQzXzdoM19iNDUzfQ==" | base64 -d
# THM{ju57_d3c0d3_7h3_b453}Answer
- Feed me the flag!
THM{ju57_d3c0d3_7h3_b453}
Meta meta
desc
Meta! meta! meta! meta...................................
solution
wget -O find_me.jpg 'https://tryhackme-vm-upload.s3.eu-west-1.amazonaws.com/Find_me_1577975566801.jpg?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Content-Sha256=UNSIGNED-PAYLOAD&X-Amz-Credential=AKIA2YR2KKQMWLXEMXW4%2F20260118%2Feu-west-1%2Fs3%2Faws4_request&X-Amz-Date=20260118T055108Z&X-Amz-Expires=120&X-Amz-Signature=1087145cb55ad17ce4dd54c8a52e16d728a4a083a5b553302b5fd5de49a34753&X-Amz-SignedHeaders=host&x-amz-checksum-mode=ENABLED&x-id=GetObject'
exiftool find_me.jpg
# Owner Name : THM{3x1f_0r_3x17}Answer
- I'm hungry, I need the flag.
THM{3x1f_0r_3x17}
Mon, are we going to be okay?
desc
Something is hiding. That's all you need to know.
Asolution
wget -O Extinction.jpg 'https://tryhackme-vm-upload.s3.eu-west-1.amazonaws.com/Extinction_1577976250757.jpg?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Content-Sha256=UNSIGNED-PAYLOAD&X-Amz-Credential=AKIA2YR2KKQMWLXEMXW4%2F20260118%2Feu-west-1%2Fs3%2Faws4_request&X-Amz-Date=20260118T055407Z&X-Amz-Expires=120&X-Amz-Signature=9d423e72b0f451a7f0422c67ba05e6d3caf08c2a08b77de738ae6ad49127f20d&X-Amz-SignedHeaders=host&x-amz-checksum-mode=ENABLED&x-id=GetObject'
steghide extract -sf Extinction.jpg
# wrote extracted data to "Final_message.txt".
cat Final_message.txt
# It going to be over soon. Sleep my child.
# THM{500n3r_0r_l473r_17_15_0ur_7urn}Answer
- It is sad. Feed me the flag.
- steghide
THM{500n3r_0r_l473r_17_15_0ur_7urn}
Erm......Magick
desc
Huh, where is the flag? THM{wh173_fl46}
solution
cukup select teksnyya aja.
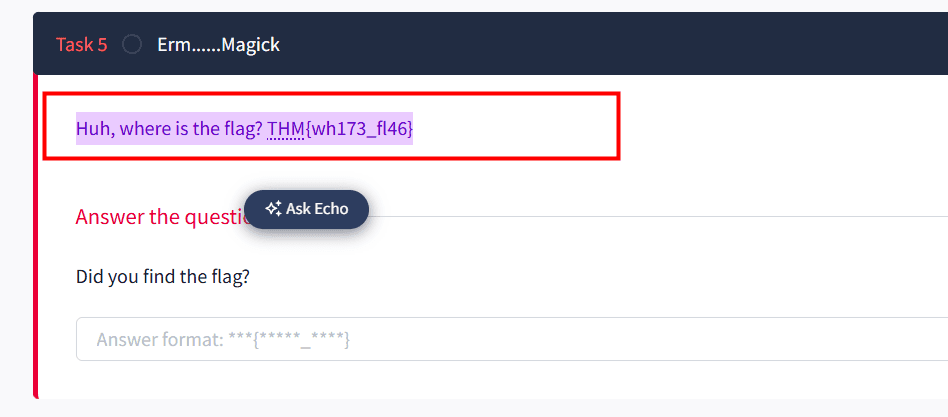
Answer
- Did you find the flag?
THM{wh173_fl46}
QRrrrr
desc
Such technology is quite reliable.
solution
wget -O qr1.jpg 'https://tryhackme-vm-upload.s3.eu-west-1.amazonaws.com/QR_1577976698747.png?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Content-Sha256=UNSIGNED-PAYLOAD&X-Amz-Credential=AKIA2YR2KKQMWLXEMXW4%2F20260118%2Feu-west-1%2Fs3%2Faws4_request&X-Amz-Date=20260118T055748Z&X-Amz-Expires=120&X-Amz-Signature=ab34875d923f2e4ca7562ef2841c20809b2ba0214b40e45142210f3f353b849a&X-Amz-SignedHeaders=host&x-amz-checksum-mode=ENABLED&x-id=GetObject'
sudo apt update
sudo apt install zbar-tools
zbarimg qr1.jpg
# QR-Code:THM{qr_m4k3_l1f3_345y}Answer
- More flag please!
THM{qr_m4k3_l1f3_345y}
Reverse it or read it?
desc
Both works, it's all up to you.
solution
wget -O hello1.hello 'https://tryhackme-vm-upload.s3.eu-west-1.amazonaws.com/hello_1577977122465.hello?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Content-Sha256=UNSIGNED-PAYLOAD&X-Amz-Credential=AKIA2YR2KKQMWLXEMXW4%2F20260118%2Feu-west-1%2Fs3%2Faws4_request&X-Amz-Date=20260118T060200Z&X-Amz-Expires=120&X-Amz-Signature=eb286385f0ecc46510d73dd65c3aabea5bd5c45d52c001838da693d7d34815c5&X-Amz-SignedHeaders=host&x-amz-checksum-mode=ENABLED&x-id=GetObject'
file hello1.hello
# hello1.hello: ELF 64-bit LSB shared object, x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, BuildID[sha1]=02900338a56c3c8296f8ef7a8cf5df8699b18696, for GNU/Linux 3.2.0, not stripped
strings hello1.hello | grep THM
# THM{345y_f1nd_345y_60}Answer
- Found the flag?
THM{345y_f1nd_345y_60}
Another decoding stuff
desc
Can you decode it?
3agrSy1CewF9v8ukcSkPSYm3oKUoByUpKG4L
solution
use base58 for decode
Answer
- Oh, Oh, Did you get it?
THM{17_h45_l3553r_l3773r5}
Left or right
desc
Left, right, left, right... Rot 13 is too mainstream. Solve this
MAF{atbe_max_vtxltk}
solution
use the caesar cipher with shift 7 for decode
Answer
- What did you get?
THM{hail_the_caesar}
Make a comment
desc
No downloadable file, no ciphered or encoded text. Huh .......
solution
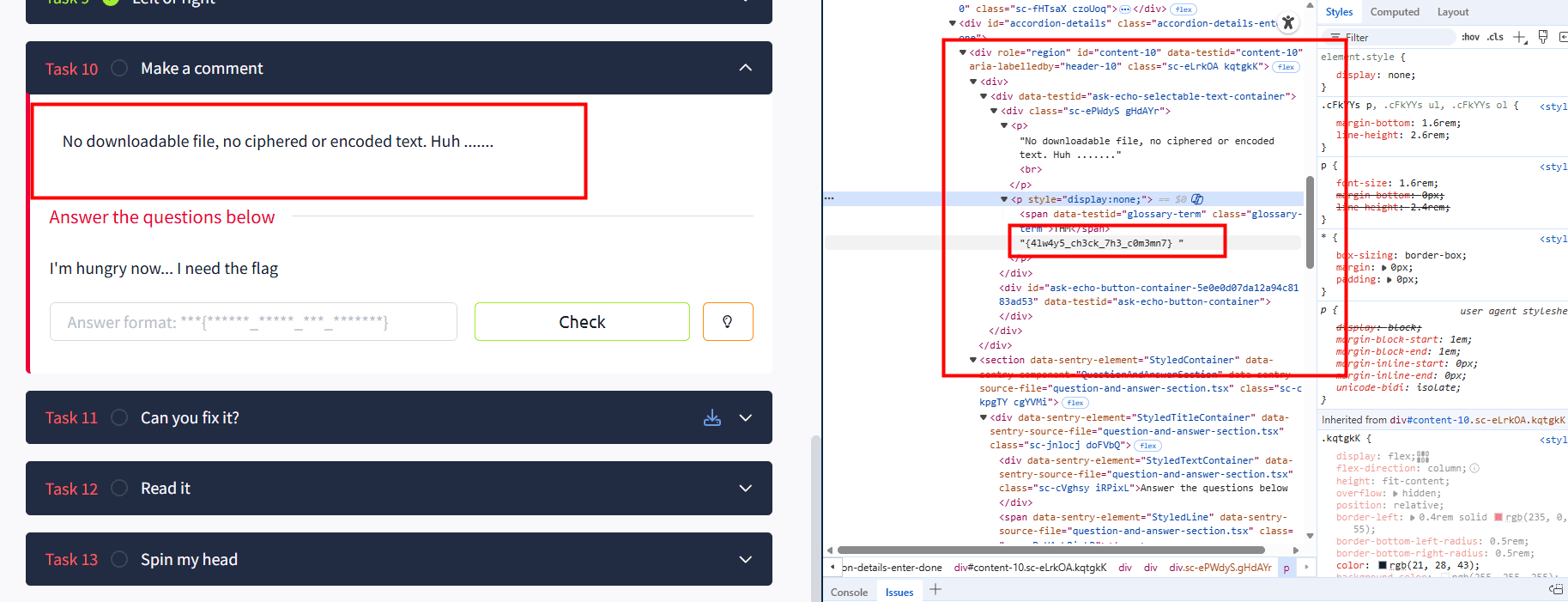
check the html in the quiz element.
Answer
- I'm hungry now... I need the flag
THM{4lw4y5_ch3ck_7h3_c0m3mn7}
Can you fix it?
desc
I accidentally messed up with this PNG file. Can you help me fix it? Thanks, ^^
solution
wget -O spoil1.png 'https://tryhackme-vm-upload.s3.eu-west-1.amazonaws.com/spoil_1577979329740.png?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Content-Sha256=UNSIGNED-PAYLOAD&X-Amz-Credential=AKIA2YR2KKQMWLXEMXW4%2F20260118%2Feu-west-1%2Fs3%2Faws4_request&X-Amz-Date=20260118T060911Z&X-Amz-Expires=120&X-Amz-Signature=fb450a10cec3cf4895edf31e4ed2db5cc865f8c9909620287e1c56fb9dc70e27&X-Amz-SignedHeaders=host&x-amz-checksum-mode=ENABLED&x-id=GetObject'
file spoil1.png
xxd spoil1.png | head
# 00000000: 2333 445f 0d0a 1a0a 0000 000d 4948 4452 #3D_........IHDR
# 00000010: 0000 0320 0000 0320 0806 0000 00db 7006 ... ... ......p.
# 00000020: 6800 0000 0173 5247 4200 aece 1ce9 0000 h....sRGB.......
# 00000030: 0009 7048 5973 0000 0ec4 0000 0ec4 0195 ..pHYs..........
# 00000040: 2b0e 1b00 0020 0049 4441 5478 9cec dd79 +.... .IDATx...y
# 00000050: 9c9c 559d eff1 cf79 9e5a bb7a 5f92 7477 ..U....y.Z.z_.tw
# 00000060: f640 4802 0920 1150 c420 bba2 88a8 805c .@H.. .P. .....\
# 00000070: 1906 7c5d 64c0 79e9 752e 03ce 38e3 0e8e ..|]d.y.u...8...
# 00000080: 2f75 e63a 23ea 8c0c e830 8e03 6470 c191 /u.:#....0..dp..
# cek gambar yang bener untuk melihat perbandinganya
wget "https://raw.githubusercontent.com/ariafatah0711/ctfs/main/images/README/image-4.png"
xxd image-4.png | head
# 00000000: 8950 4e47 0d0a 1a0a 0000 000d 4948 4452 .PNG........IHDR
# 00000010: 0000 06ca 0000 0401 0802 0000 000c d248 ...............H
# 00000020: d800 0010 0049 4441 5478 01ec 5d05 8024 .....IDATx..]..$
# 00000030: c5d5 7eaf 7b6c dd6e cffd e038 ced0 c30e ..~.{l.n...8....
# 00000040: 7777 770b 1648 084e 0209 0192 10fb 4312 www..H.N......C.kita cek di list of signature file png itu harusnya mulai dengan
89 50 4E 47 0D 0A 1A 0A
kita coba ubah dengan hex editor
hexedit spoil1.png
# 89504E470D0A1A0A
file spoil1.png
# spoil1.png: PNG image data, 800 x 800, 8-bit/color RGBA, non-interlacedtinggal di buka di image viewer
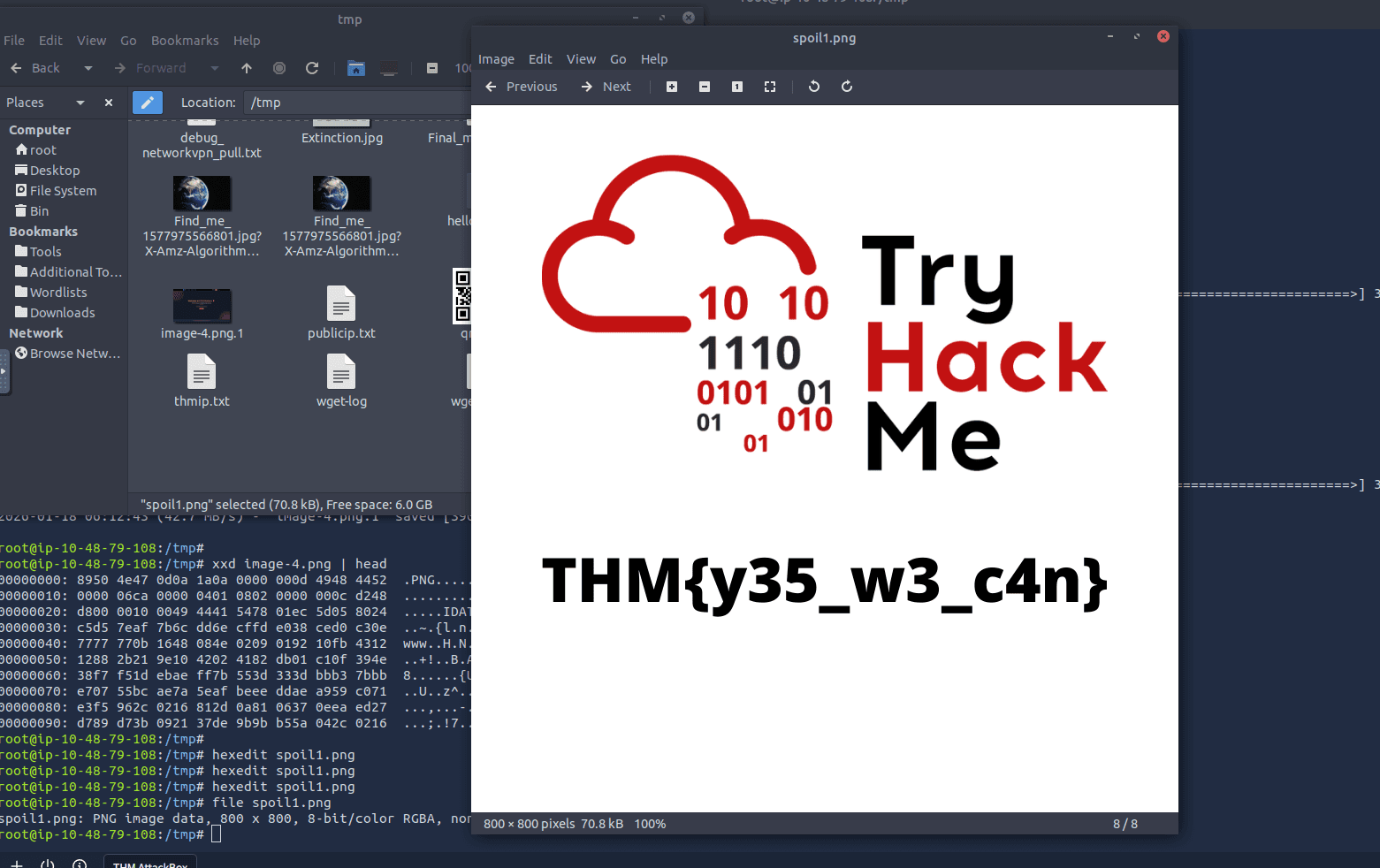
Answer
- What is the content?
THM{y35_w3_c4n}
Read it
desc
Some hidden flag inside Tryhackme social account.
solution
cari ini di google tryhackme rooms reddit atau inurl:”reddit.com” &intext:”THM” & intitle:”tryhackme”
namun ketika di cari susah jadi saya liat writeup aja untuk yang pertanyaan ini. dan ternyata ada 1 gamabr yang di post di reddit yang berisi flag..
intinya kita cari di pencarian reddit dengan keyword new room
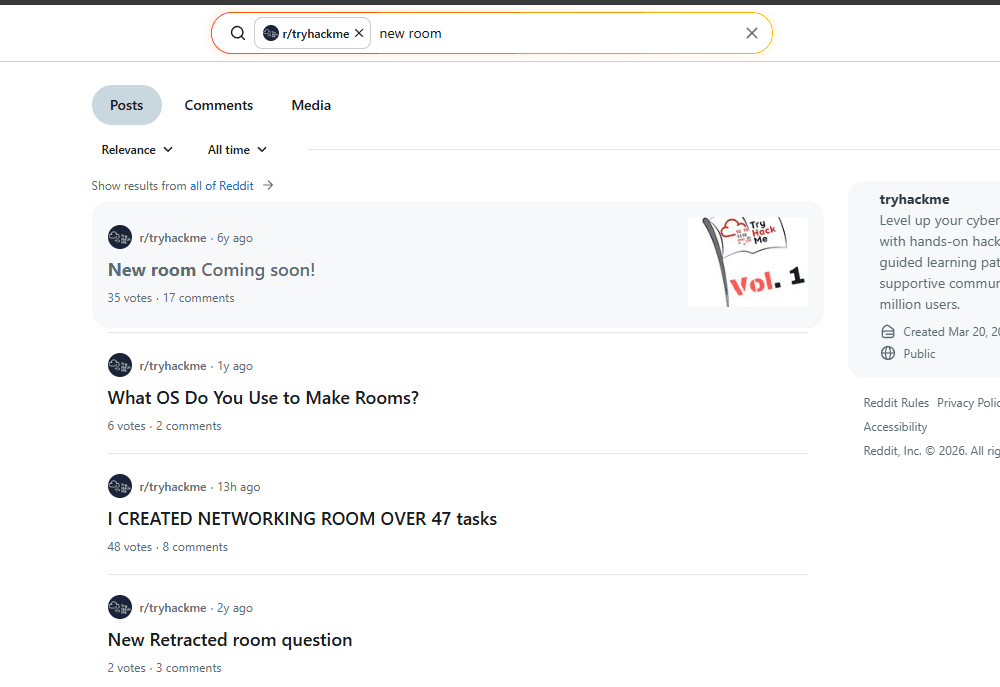
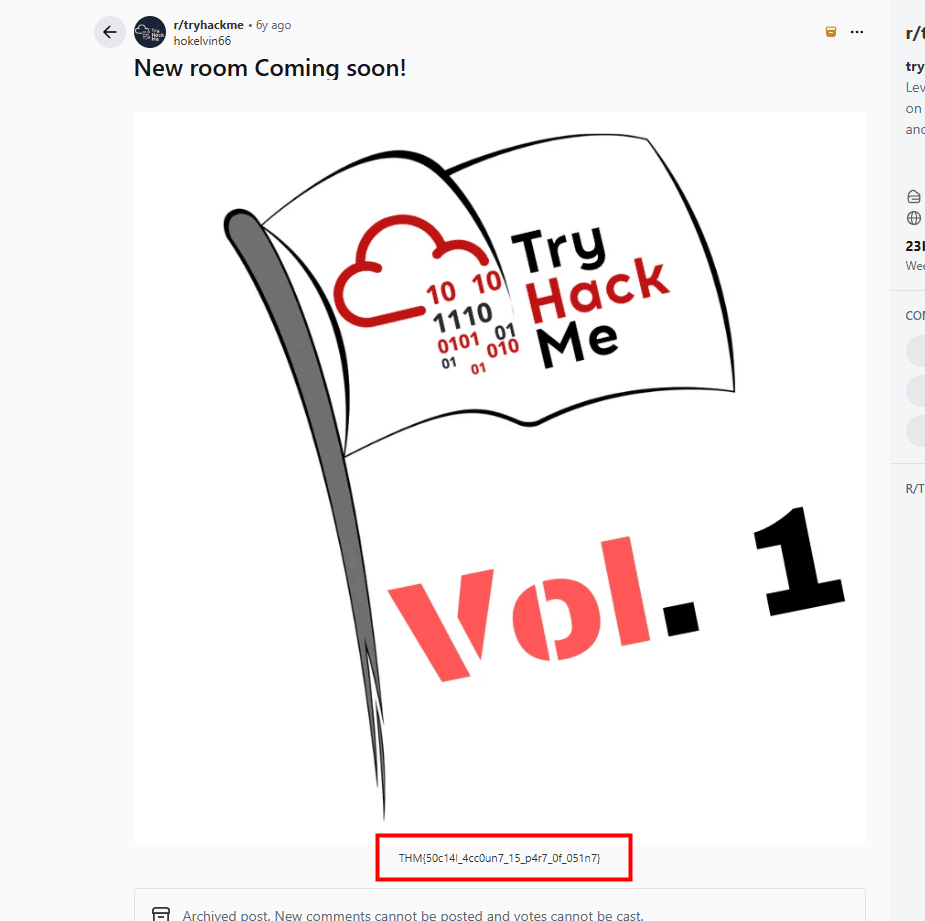
Answer
- Did you found the hidden flag?
- Reddit.
THM{50c14l_4cc0un7_15_p4r7_0f_051n7}
Spin my head
desc
What is this?
++++++++++[>+>+++>+++++++>++++++++++<<<<-]>>>++++++++++++++.------------.+++++.>+++++++++++++++++++++++.<<++++++++++++++++++.>>-------------------.---------.++++++++++++++.++++++++++++.<++++++++++++++++++.+++++++++.<+++.+.>----.>++++.solution
jika di lihat ini sepertinya menggunakan brainfuck
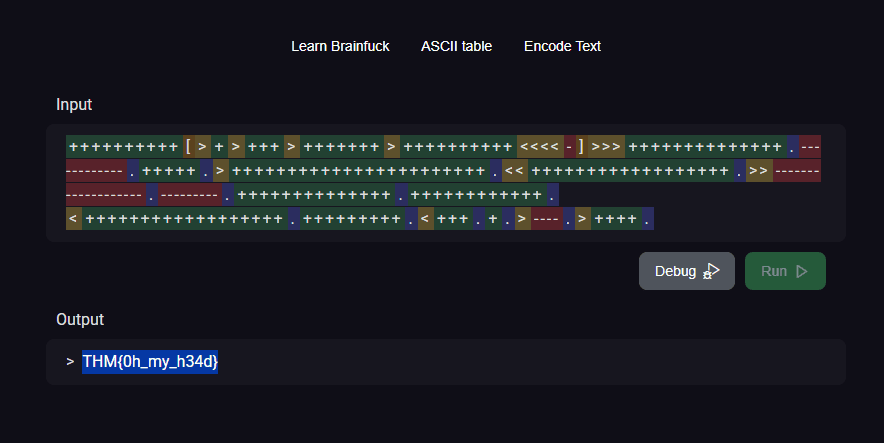
Answer
- Can you decode it?
THM{0h_my_h34d}
An exclusive!
desc
Exclusive strings for everyone!
S1: 44585d6b2368737c65252166234f20626d S2: 1010101010101010101010101010101010
solution
lakukan xor antara S1 dan S2, dengan hex karena sepertinya keduanya merupakan hex.
Answer
- Did you crack it? Feed me now!
- S1 XOR S2
THM{3xclu51v3_0r}
Binary walk
desc
Please exfiltrate my file :)
solution
wget -O binary_walk.jpg 'https://tryhackme-vm-upload.s3.eu-west-1.amazonaws.com/hell_1578018688127.jpg?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Content-Sha256=UNSIGNED-PAYLOAD&X-Amz-Credential=AKIA2YR2KKQMWLXEMXW4%2F20260118%2Feu-west-1%2Fs3%2Faws4_request&X-Amz-Date=20260118T063125Z&X-Amz-Expires=120&X-Amz-Signature=cfd6ef4e94ef4e0360d8a5bec393648b6af85dd581c4c4e47a335585c8b3a44b&X-Amz-SignedHeaders=host&x-amz-checksum-mode=ENABLED&x-id=GetObject'
foremost binary_walk.jpg -T
# Processing: binary_walk.jpg
# |foundat=hello_there.txtUT
# *|
cd output_*
ls
# audit.txt jpg zip
cd zip
ls
# 00000519.zip
unzip 00000519.zip
cat hello_there.txt
# Thank you for extracting me, you are the best!
# THM{y0u_w4lk_m3_0u7}Answer
- Flag! Flag! Flag!
THM{y0u_w4lk_m3_0u7}
Darkness
desc
There is something lurking in the dark.
solution
wget -O darkness.png 'https://tryhackme-vm-upload.s3.eu-west-1.amazonaws.com/dark_1578020060816.png?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Content-Sha256=UNSIGNED-PAYLOAD&X-Amz-Credential=AKIA2YR2KKQMWLXEMXW4%2F20260118%2Feu-west-1%2Fs3%2Faws4_request&X-Amz-Date=20260118T063539Z&X-Amz-Expires=120&X-Amz-Signature=c3d8607c18ca5d760affccd6ed1699e2fa8371bb6f29f505b65897d0f3d49f1c&X-Amz-SignedHeaders=host&x-amz-checksum-mode=ENABLED&x-id=GetObject'disini saya coba gunakan tools cyebrchef untuk mencari bitplane
https://gchq.github.io/CyberChef/#recipe=View_Bit_Plane('Blue',1)&input=iVBORw0KGgoAAAANSUhEUgAAA8gAAAEsCAIAAACQeg3oAAAAAXNSR0IArs4c6QAAAARnQU1BAACxjwv8YQUAAAAJcEhZcwAADsMAAA7DAcdvqGQAABAWSURBVHhe7daNjhu5jgbQwe77v/MSlxeEVqU/l8uepPscCAVb%2BkixO5PK/AMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAXP3vf9b//Gc9ohryV/Dn9Wv9mD/6f%2BsH%2BTG/wGfl7yRWfAD4XeoNmOsR9Y%2BNt%2BpfwZ/Xr/Vj/ujzp3jqDXbux/wCn1V/HH4zwH%2B174XD1Tp/1S6S7QwnrVqRr/J1bcU6bYft6q6o2m7/XHWo/rdbDX26/0zdu70uY4v14MDnUy1UkxrvnW5bX76u1L3fue5EjXSyurGrtts/Vx2q/%2B1W76gZTrQzvzlttXqzz0vq0voRtre3%2BeGadbhdGKoWYP82ua72/ZLlizdOisAimUe1tt1aXe3CbIDY6ZosVldetd3%2BifWlNxp2Pt1/ob16e9F6zlgPjhqt8rp7Pat8uB63uCvWvR/hUHv1Ry96SUyy/p20qxu7arv9E%2BtLbzR8Rw1zopv8HdEqu33n5%2B0m79ZihnVhrFnt7cIQR1kO8N83wnXVq%2BS6WvF1/cZJWThL5lGtbbfSFcaaiWSGh/J0vbJ/fGjVUbe/VQ2ztlZtxnrHp/vPXG%2BJr2uZz8LhelA2PJnqKgtrZatu80Ft57rrc9eV6y3x9c%2BR463XcOw66va3qmHW1qrNWN9UV291Q56ULNRPHc9PayfPe3PVZqyZjLVV3ZqJo3uFKQJZDjCQ74jFy6scvk0isEjWUX44uTedF1bmnln/ahvPl2ThUDa80bP16f5D1Tmb59ftLRn7jvOprrJwOGod3Wg7E61m3T5xXarO2Ty/Pn7LR9WP0Ln942ThUDb88q%2BoLt3KZDzPSxaqTzw/Le8ayhkWY2TghtuFKctnUwG/Xb4jTt4yh2%2BTCCyS7dEi1olMhvNzfMjPQ234VVUbz87i6LbqeW/arQ/1r57xIb/mTn5dyNh3nE/VyapFYQW%2BIO76xHXdz1i35Ne/wmLmxdFt1TPW1xze2P6wjwwZTdqe/5YaY/bj5OkNtwtTlscTYGD95modvk0isEi2R/n51au3VRHIzA2L5tU2ng9a3PiIT/TPniW%2B5k4817rCjzqfqpNVizkr8Grne7bz3JA9S3zNne/8RI9Y/Fo%2B9OMsbvyQkxvrh02PDFk94/nvWv84eXrD7cL0h/xygD/U%2Bs3VOnybRGCRbI/y82HPa9VMBDLzqiqM59X1tHZmJSeqw1X1LzeuW/S/rbs9vuYt26ky9h3XqWpnMWplZoEwy9R%2BqZ0Mx7qhOjyomyRnyyEXKlZqZ1v7rLp3eOn1tHbembM6fMJwwpMbM3NYEqcZKJWvDqFi7WapklaVlNqZ9TlRHYa6G8/dLkxZfvuHAn649Zurdfg2icAi2R3l1/XtXWZbEoHMvGrdudrGM79muF15dK6aDAtjMwP5OZO1Tqz7P6Xm3N6Sse/opsrP3cqjVsXW2s4lvuZ%2Bqlbt6kq2qsmrhS%2BJ5nnR%2BpaKtZ%2B7te7wlLp6qGbLYSrcrjw6V01eLdwajherPZq5BtYlcZqB/JzJWqVi8exUVXdUJe3nbnUlW9VkVpiBG24XpiyfTQX8dvmOOHnLHL5NIrBIdkf5dX37qyUnPYfWhXFagVq52e7H50Nt4VAFKpY7ubYytuj/lLpoO9Vh7BE1Vbtys92Pz606WhvGqnN9qM/1NXcOtYUfVRetZ2tjOVV%2Brv3a%2BbS6bqibJ1dutvvx%2BVBb%2BKxunlq1mWsmk/EsVTtUzSuWO7lKfs3TVm5e90Nbkpn8XPu1c6gtnMnAec9yuzC9WQ78cPmOWLy8SiXjw3pV7CpP26PrTitPY5XrTmcbGKqqxSSVucbao622Vden1cZO2pbD/k%2Bp67Z31VTX9ficNdWwf3vUqv21YSw227bxuVOn16NO22obfl9dt76rYsPB2qOPqou6AUrst8N0sfZoq23V9Xlf27zTHl1PUwbi2Zo1TCdtQ8XiWaqw3SxVMsy0R1ttq65Pp23brQ8Vpiw/SQK/Ub1ithYvo%2BEavneur6T1AK/mw7XkxEnbdebwtFY2XMhAhdcqWSvLvyAvyhvXMrZYD6qpZm2Hp%2BuSMqvd3piBeF5Vba3Mf0FelDcuVCzW0Pr0Kdtb3pyzTmtlw8dtx1gE6rRz3jM%2BzFSsMtuqKok1dHhaKxuuXau6NXO7MFU5wMD5O2L7MupW5K%2BySXtUba/52MnTVuWvKj88Xaiq%2BDBTzWeZajJUp9e1aJhVs0DrRv%2BnvDTnVZXnesp2qrq0Ndy8mtXmfjxnFv3r6LoWDR8R/fP29UXbWJ7G%2Bpy6YjZDiKOMzTLVZKhOr2vW8J71GGERyKPrPOuecTorbHWx/Lyu6kquqslQnV7XrOFM5Ntu584L22R8APh/6gWxlcnteyQCi%2BTwKDevMwz3t%2BGu%2BYlZz1ZkMjbrvw10MpxrWPJqw862/1PenDPVtE%2BNup1qGMidWGvD2LBh57B/qvC65/uied61vmUb2wbel/1jLWzH2AY6Gc51WLJ1MkPd25nth8VRiNMMxHOhjeWHl0qGtoFOhk%2BuHqryV2sPC%2BP09hXAD1dvh61Mbl8iEVgkh0e5eZ3hRvia3zosjNNMzmLbwFWVDKvq9Hp0qDq802Srbnnzihr1EduphoHc2c4wjA0bdg77l%2Bq5bvumumV9xTa2Dbwpm/8rc1bJS1UL1XDRrW7sLApnJSlOF7WlYu1a23beBq6q5KWqUrWvOix8ZzbgJzt/%2B2Ry%2BxKJwCI5O7ru506szmw/rU%2BHDksilsl4Dm0DQ1kyHOBew86i/1MemTPUqI/YTjUM5M52hmFs2LBz2L9VJS9VveRk8rCNbQNvyubb38N2jG1gKEtOBjhR3RYzVKaVm7OqYUmJ03V5amP54aWSoW1gKEtyvapqX3VSeLs58POdvyAyGc%2B1CCySs6Pcb8c4T3ZmhUMRO8xvk9vATFbF6txu2Jn1f8qfOed2qmEgd7YzXAtDfB3utzKw7d%2B5V3XuZPKwjW0D7zhvvk1uAzNZFet9JzMMr6uq2cqS%2BtqqQLff6WL5eV3VlVxtAzNZFetVnyu83Rn4Fc7fEZmM51oEFsnZUe7XUX29WhylbaDV3bsQgQzPktvATFbF6txu2Jn1f8qfOed2qmEgdxZVYVgYZvutDMR6yb2qcyeTh21sG3hHdj5pvh1jG5jJqljvO5nhel1Vna9Wlcdz4RrLr1231rWksw3MZNXi6pnPFd77QYDf4vztc/g2icAiuT3KSQ5jQ9tA6zwcyQzHc2gbGKqq6wz3GnYW/Z/yyJzh2Tm3U80C66qQgeucsX%2B7dqHavlT1kroingvb2Dbwjux88kvYjrENDFXVyQwntjMMr6vNw9WK2u2l4Rqrna5huZZ0toGhqprdu/C5wgzEE2Dg/O1z%2BDaJwCK5PWrXOjYTgcxsVavhRZ1qOwtvA0NZMqy617Cz6P%2BUP3PO7VSzQG7GmpkFquGstk7jw7l7VS%2BJznnL%2BoptbBu4Ldsedt6OsQ0MZcmrVQvVcChO14Ghw57xXBjGcmdWOyxpbQNDWfJqVfhoYWZe7Qz8FvUe2Tp8m0RgkVwf5WmtocrMVJ%2BtbatWtY3n0DCQmzOZn82QtYsbQ2ZmsnzW/yk5w582Z964mGoWyM3ZMHXaVYXYaWu7QHvayv2ZKumqnlWzLSYJ29g2cFu2PfwlbMcYBnJzJvPnM5xY9MxhZqcLVTVUbeO5MIvl5rB8VlKGgdycyXyuzvcLWxlb9AF%2BtXqVbB2%2BTSKwSK6b5GmubWYmAplZqz6zizrVdpYfBmqz7qpVm7l/VbHhaapM9alVm7n/oPaWXHVLu1q5M4zlZq4HVfN4Di0CuZ8rY7nazasuU8luPz63rqe1ajP3H9TekqtuaVcnNxfDbAP3ZM/zttsxhoHarLtq1WbuP6htXtfVZn0%2BV7VD1TCeC4tY7l%2BPFiVpGKjN6lmrNnO/02byc62qinXVZqqk3cy1luF4AgzUC2Xr8G0SgUVy3SRPc81UZiYCmVnb9ulU23gOzQK5uVivNuzc7n/b9sZcnXXVJ4bMG2ed14E8Gq6ThvW5W7F5NUy2a1j1ju2NuTpRlYWzebaBe7LndZ6Z7RizQG4u1qzhO2aXpjw9V92G4jQD8VxYxOqou2JRkmaB3FysRcMu2a5ZVbhdWLLDSRL4jeots3X%2BNlkkt00OA7FmIpCZhcrE89C27TqQpxnIlV8XKn8iw5k/7H9be8tiDX1zyLxoZhsIlalpFypcsdrZ1oYMVz5LtlX3tLcsVqfGm9kGbqie8Ty0HWMdyNMM5Mqvn9Ne192V%2B%2Beqz1A23zZcx%2Bo0nmVdEtaBPM1Arvy6da8q3C4MWXieB/i75SsyXnzwTfUfnn9x4Qfz1xz4Xer/b%2BCb6j88/%2BLCD%2BavOfDr5IsPvin%2Bq/MvLvxs9dcc4BfJF593H99U/%2BLGE/h56u%2B4f1yA36Xefd6AQ93v53B9398yZ6p/dOP5af4E/xA//gektH/WX/g7DvBniRdfvQfp/C3/N/C3zJnqP7kv8Cf4h/jxPyCl/qzjAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAPyl/vnn/wD9XirDJa31YQAAAABJRU5ErkJggg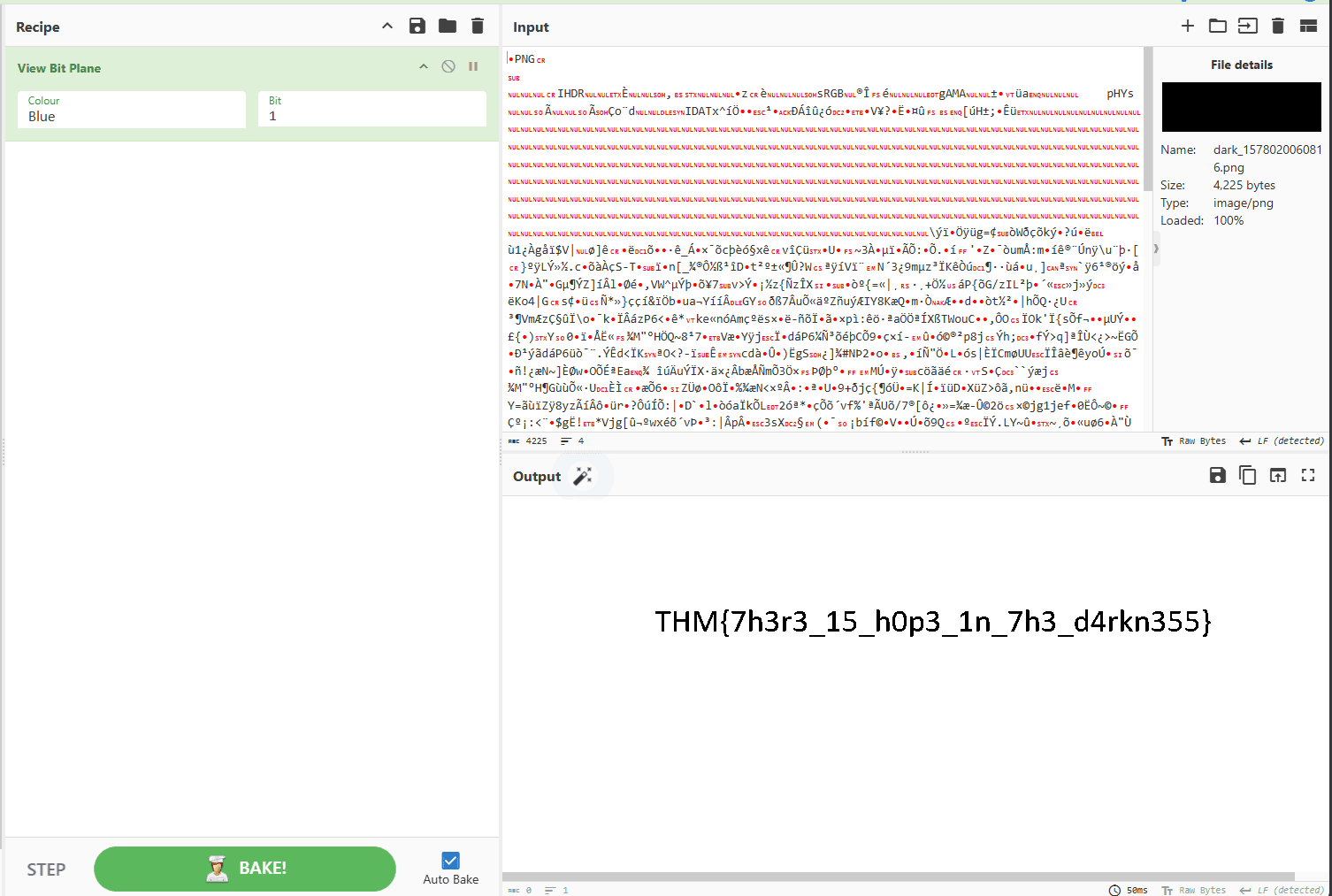
Answer
- What does the flag said?
- Try stegsolve.
THM{7h3r3_15_h0p3_1n_7h3_d4rkn355}
A sounding QR
desc
How good is your listening skill?
P/S: The flag formatted as THM{Listened Flag}, the flag should be in All CAPS
solution
wget -O qr2.png 'https://tryhackme-vm-upload.s3.eu-west-1.amazonaws.com/QRCTF_1579095601577.png?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Content-Sha256=UNSIGNED-PAYLOAD&X-Amz-Credential=AKIA2YR2KKQMWLXEMXW4%2F20260118%2Feu-west-1%2Fs3%2Faws4_request&X-Amz-Date=20260118T063954Z&X-Amz-Expires=120&X-Amz-Signature=0b9513f120351d2860bc856aff7db7b033885b34cd200ab58f37547ad164406a&X-Amz-SignedHeaders=host&x-amz-checksum-mode=ENABLED&x-id=GetObject'
zbarimg qr2.png
# QR-Code:https://soundcloud.com/user-86667759/thm-ctf-vol1setelah itu dengerakan musicnya, namun jika ingin cepet bisa cek comentar aja yang udh memberi tau flagnya
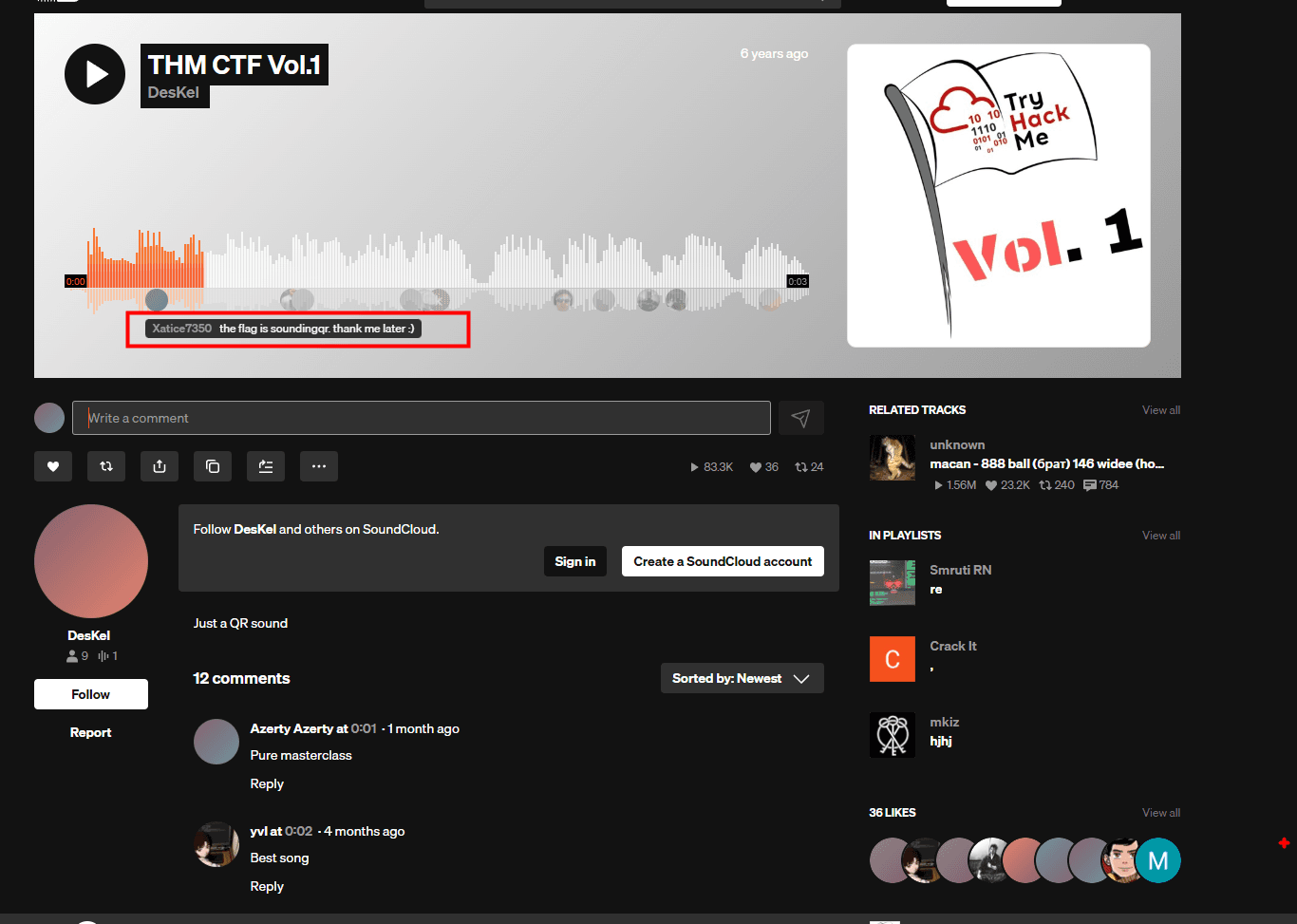
Answer
- What does the bot said?
THM{SOUNDINGQR}
Dig up the past
desc
Sometimes we need a 'machine' to dig the past
Targetted website: https://www.embeddedhacker.com/ Targetted time: 2 January 2020
solution
gunakan web archive untuk melihat web di waktu yang di inginkan
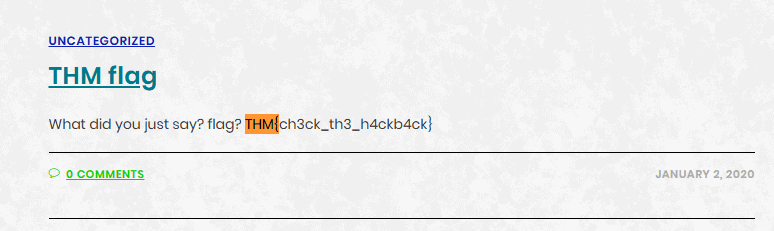
Answer
- Did you found my past?
- Wayback machine
THM{ch3ck_th3_h4ckb4ck}
Uncrackable!
desc
Can you solve the following? By the way, I lost the key. Sorry >.<
MYKAHODTQ{RVG_YVGGK_FAL_WXF}
Flag format: TRYHACKME{FLAG IN ALL CAP}
solution
jika dilihat ini sepertinya menggunakan vigenere cipher
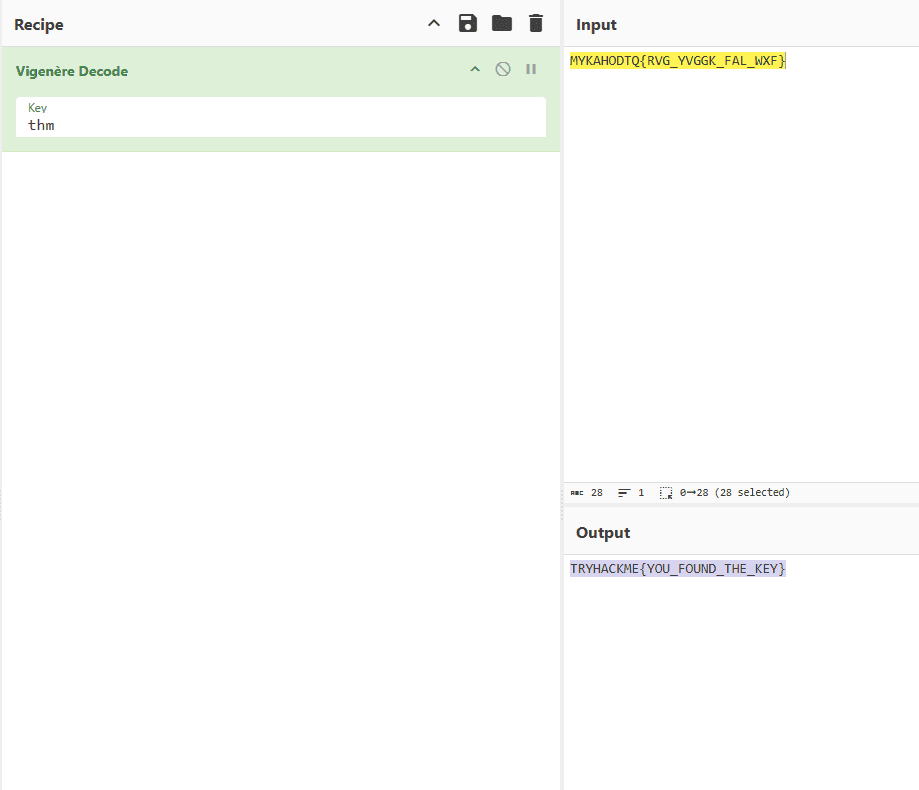
Answer
- The deciphered text
- Find the key of vigenere cipher
TRYHACKME{YOU_FOUND_THE_KEY}
Small bases
desc
Decode the following text.
581695969015253365094191591547859387620042736036246486373595515576333693solution
DECIMAL → HEX
python3 - << 'EOF'
n = 581695969015253365094191591547859387620042736036246486373595515576333693
print(hex(n)[2:])
EOF
54484d7b31375f6a7535375f346e5f307264316e3472795f62343533357dHEX → ASCII
echo "54484d7b31375f6a7535375f346e5f307264316e3472795f62343533357d" | xxd -r -p
# THM{17_ju57_4n_0rd1n4ry_b4535}Answer
- What is the flag?
- dec -> hex -> ascii
THM{17_ju57_4n_0rd1n4ry_b4535}
Read the packet
desc
I just hacked my neighbor's WiFi and try to capture some packet. He must be up to no good. Help me find it.
solution
wget -O hack.pcapng 'https://tryhackme-vm-upload.s3.eu-west-1.amazonaws.com/flag_1578026731881.pcapng?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Content-Sha256=UNSIGNED-PAYLOAD&X-Amz-Credential=AKIA2YR2KKQMWLXEMXW4%2F20260118%2Feu-west-1%2Fs3%2Faws4_request&X-Amz-Date=20260118T065812Z&X-Amz-Expires=120&X-Amz-Signature=41389e775ec5f3987dd0de82f5a768575043d469e11ce0044a307f7ee6873945&X-Amz-SignedHeaders=host&x-amz-checksum-mode=ENABLED&x-id=GetObject'
tshark -r hack.pcapng
wireshark hack.pcapng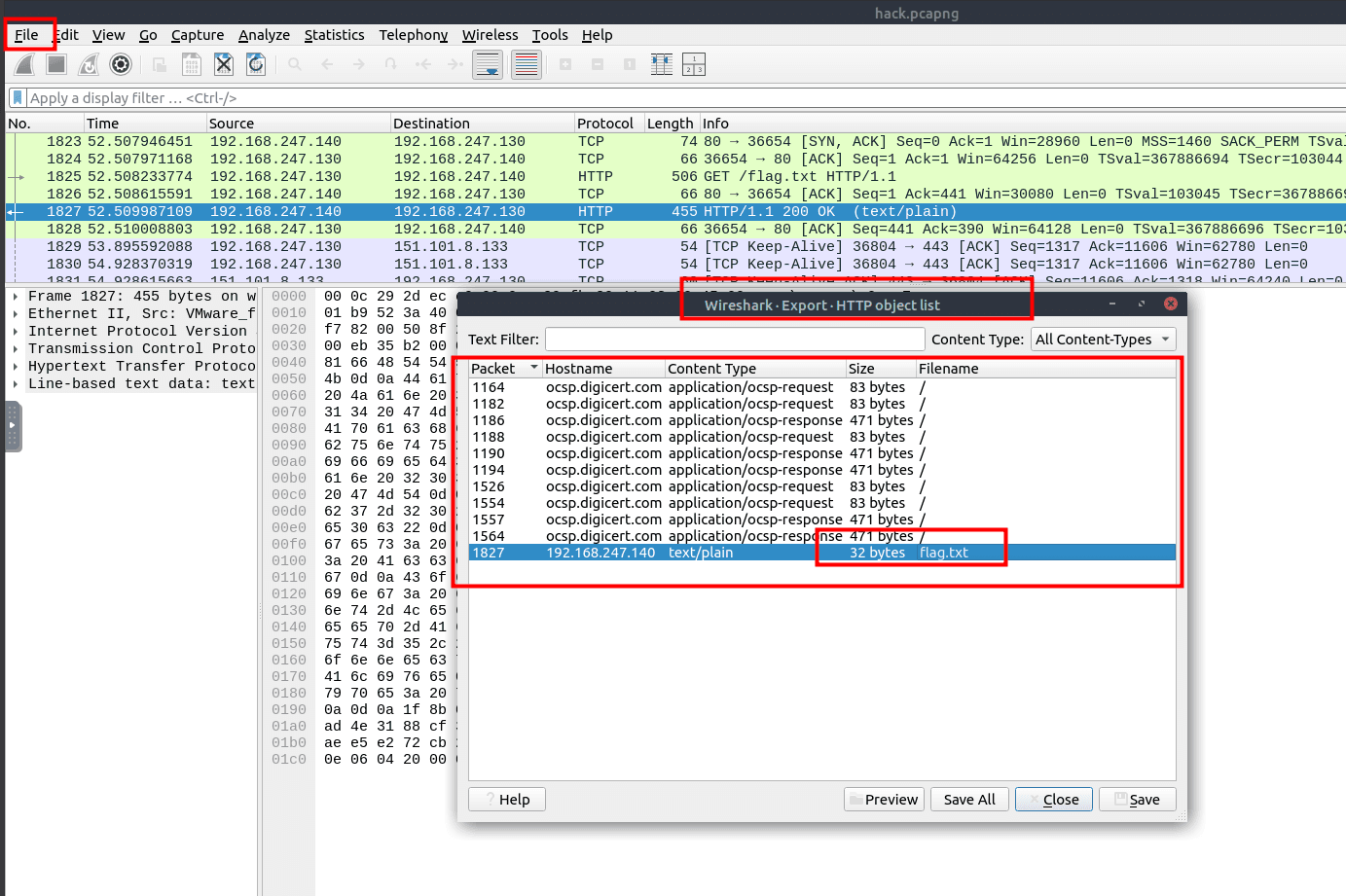
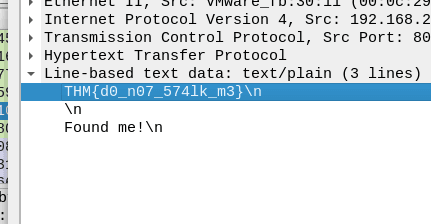
Answer
- Did you captured my neighbor's flag?
- Put it into stream. It will be much easier.
THM{d0_n07_574lk_m3}